The eight surfaces
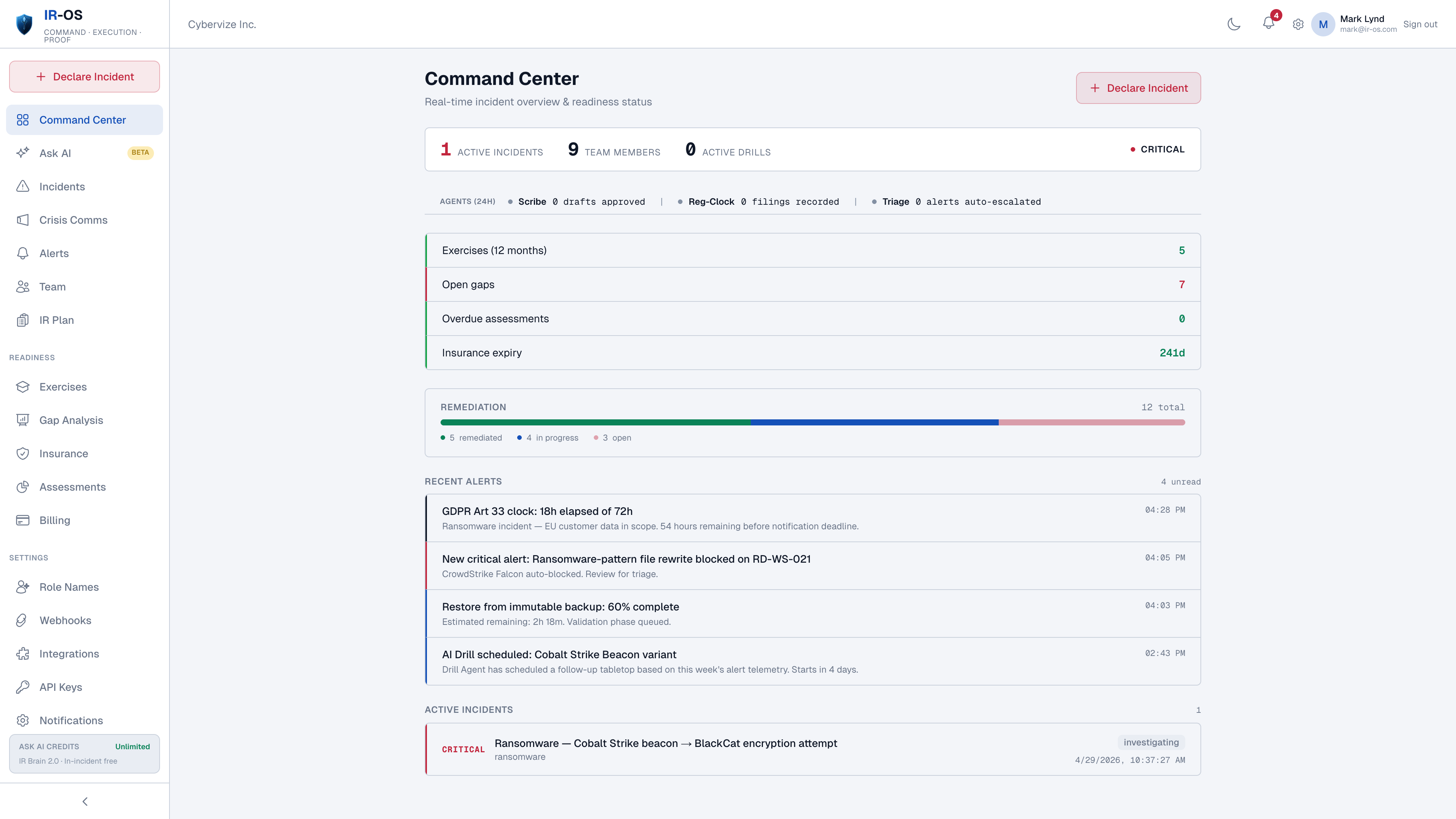
Command center dashboard
Readiness traffic lights, active-incident state, regulatory clock countdowns, role assignments, next valid actions per role.
AI-coached IR plan
15-minute conversational interview generates a complete plan mapped to NIST 800-61, ISO/IEC 27035, your regulators, and your insurer.
Six IRC roles
Incident Commander, Scribe, Communications Lead, Legal Liaison, Technical Lead, Executive Sponsor. State + Role = View.
Conditional runbooks
Ransomware, BEC, exfiltration, insider, supply chain, cloud compromise. Branches captured in the record.
Crisis communications
Stakeholder map, holding-statement library, channel-scoped privilege, hash-chained sign-off trail. Watermarked SAMPLE exports for tabletops.
Parallel regulatory clocks
GDPR, HIPAA, SEC Item 1.05, NY DFS, NIS2, DORA, state breach laws, cyber insurance first-notice. Each from its own start event.
Auto-generated AAR
Eight-section AAR: summary, timeline, what worked, gaps, SLA compliance, regulatory status, recommendations. Gaps flow into the remediation tracker.
Hash-chained record
Append-only event ledger, SHA-256 chained, Ed25519-signed at closure, third-party verifiable at /verify.
Ask AI (citation-grounded)
Every answer cites the source - NIST section, GDPR article, your plan paragraph - so the team can verify before acting. Active incidents bypass metering.
The integration story
IR-OS does not replace the detection stack. EDR keeps detecting. SIEM keeps correlating. SOAR keeps automating. What changes is the layer above: the moment an alert is classified as security-flavored and a cyber incident is declared, IR-OS owns the command surface. Webhooks connect the layers. Slack and Microsoft Teams integration captures conversation into scoped, privilege-aware channels. The record is one-click exportable for the audit committee or regulator inquiry. Nothing the security operations team relies on goes away; the coordination layer that was missing gets added.
Common questions
What cyber incident tools does IR-OS include?
Eight surfaces in one platform. Command center dashboard with readiness traffic lights and active-incident state. AI-coached IR plan generator. Six pre-defined IRC roles. Conditional scenario runbooks. Crisis communications with privilege chain. Parallel regulatory clocks. Auto-generated 8-section AAR. Hash-chained defensible record. The IR Brain (RAG knowledge base) is grounded in NIST 800-61, ISO/IEC 27035, MITRE ATT&CK, SEC Item 1.05, GDPR, and 150+ tabletops.
Is this a SIEM, SOAR, or EDR replacement?
No. SIEM, SOAR, and EDR solve detection and technical automation. IR-OS solves human coordination, regulatory clocks, and the defensible record. The two layers complement each other. EDR fires the alert, IR-OS coordinates the response, the regulator notification, and the audit trail. Webhooks connect the layers; the data shapes are different.
What does Ask AI do during an incident?
Ask AI is a citation-grounded assistant that answers questions like 'do we need to file an 8-K' or 'what is the GDPR Article 33 trigger here'. Every answer cites the source by bracketed reference - NIST section, GDPR article, your IR plan paragraph - so the team can verify before acting. Active incidents bypass the monthly Ask AI credit limit so a real incident is never blocked by metering.
Can the team use IR-OS without configuring it first?
Yes. Five-minute setup yields a working IR plan, default IRC roles, runbooks, regulatory clocks, and the dashboard. The defaults reflect what 150+ tabletops show works. Power users can customize any of it. First-time users get a working response without choosing twelve settings under pressure.
What about after the incident closes?
Auto-generated 8-section AAR (executive summary, timeline, what worked, gaps, SLA compliance, regulatory status, recommendations). The hash-chained ledger seals at closure with an Ed25519 signature. Gaps flow into the gap analysis tracker for remediation. The next tabletop is scheduled. The record is exportable for the audit committee, regulator inquiry, or D&O carrier.