The five things every breach response toolkit needs
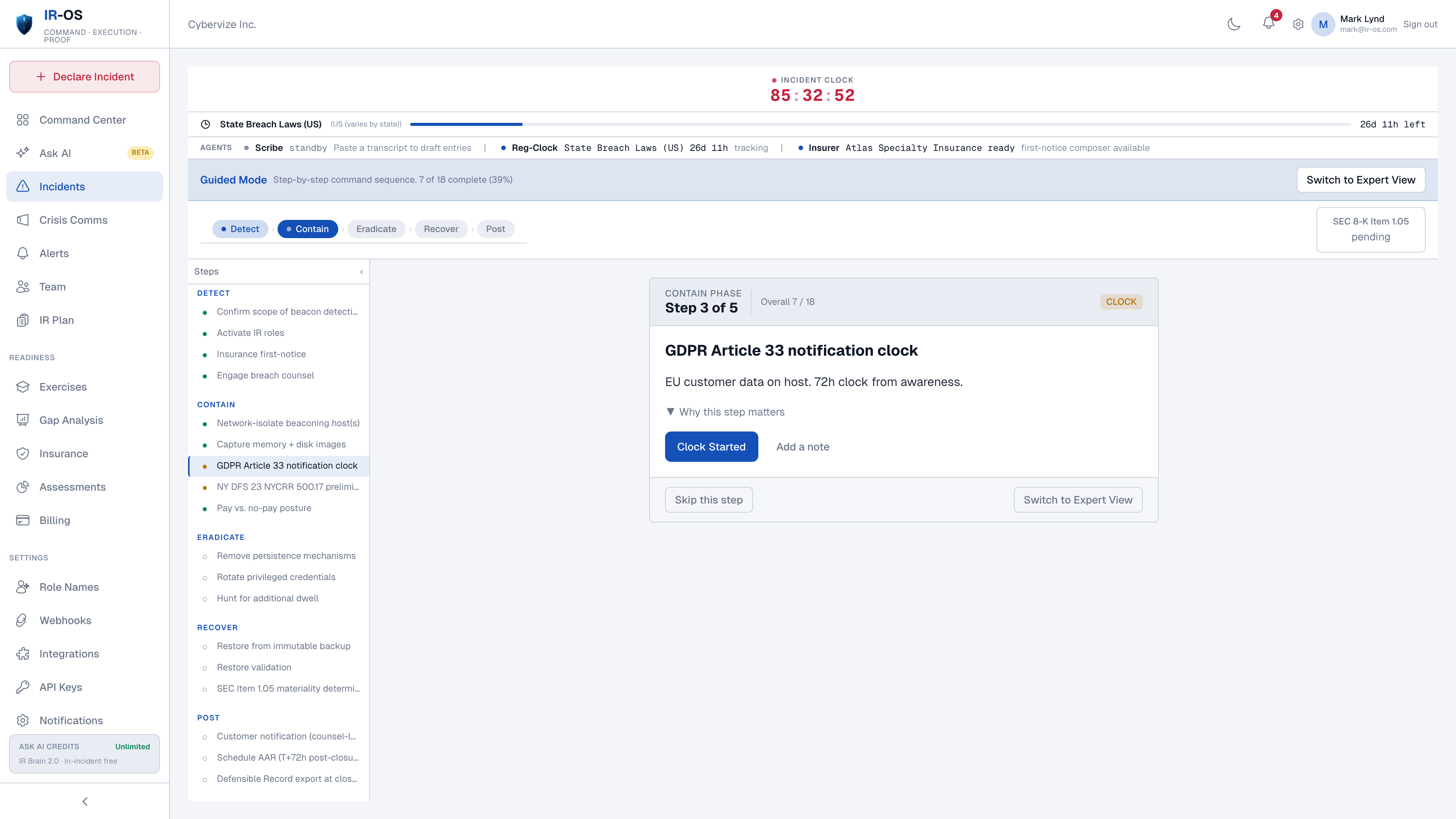
Scenario runbooks
Ransomware, BEC, exfiltration, insider, supply chain, cloud compromise, data breach. Conditional branches. The path taken is captured in the record.
Crisis communications
Holding-statement library, stakeholder map, channel-scoped privilege, hash-chained sign-off trail. Watermarked SAMPLE exports for tabletop. Privileged drafts under counsel review.
Parallel regulatory clocks
GDPR Article 33, HIPAA, SEC Item 1.05, NY DFS, NIS2, DORA, state breach laws, cyber insurance first-notice. Each from its own start event.
Panel firm directory
Breach counsel, forensics, PR, notification vendor. Surfaced in workflow at the moment they are needed. Engagement events captured in the record.
IRC roles
Six pre-defined roles: Incident Commander, Scribe, Communications Lead, Legal Liaison, Technical Lead, Executive Sponsor. State + Role = View.
Defensible record
Append-only event ledger, SHA-256 chained, Ed25519-signed at closure, third-party verifiable at /verify. The artifact every audience asks for.
The toolkit philosophy
Most breach response toolkits collect features. IR-OS collects defaults. Every workflow on this page has a default behavior the team gets without configuration: the runbook fires when the incident is classified, the regulatory clocks start at the right events, the panel firms appear at the right moments, the record writes itself. Power users can override anything; first-time users get a working response without choosing twelve settings under pressure. That default-behavior model is the difference between a toolkit that helps during an incident and a toolkit that needs ten hours of pre-incident configuration the team never finishes.
Common questions
What are breach response tools?
Breach response tools are the software a cyber-IR team uses to coordinate humans during a breach: runbooks for the standard scenarios (ransomware, BEC, exfiltration, insider, supply chain), crisis communications for stakeholder messaging, regulatory clock tracking for notification obligations, a panel-firm directory for counsel and forensics, and a defensible record for what happened and when. IR-OS bundles all five into one command surface.
How is this different from EDR or SIEM?
EDR and SIEM are detection and technical-response tools. Breach response tools are coordination tools. EDR detects malicious activity on the endpoint. SIEM correlates events. Breach response tools answer the questions that come after detection: who is doing what, what gets sent to the regulator, when does the carrier first-notice clock fire, and what record do we hand to outside counsel on Day 30. The tools are complementary, not substitutes.
Are runbooks rigid playbooks or flexible templates?
Runbooks are scenario templates with conditional branches. The ransomware runbook branches on whether the data is encrypted, whether the attacker is on the OFAC list, and whether the carrier requires pre-payment authorization. The BEC runbook branches on whether funds have moved. Each branch is captured as part of the incident record so the AAR shows which path was taken and why.
Does IR-OS replace breach counsel or forensics?
No. IR-OS surfaces the panel firm directory at the moment they are needed in the workflow and captures the engagement event. Counsel and forensics work in their own tools. IR-OS records the engagement, the privilege scope, and the deliverables. The platform makes the experts more effective; it does not try to replace them.
What artifact is produced at the end of a breach response?
A complete, append-only, SHA-256 hash-chained, Ed25519-signed record covering the full incident lifecycle. Decisions, determinations, regulator submissions, carrier first-notice, panel-firm engagements, AAR, and gap remediation. Verifiable at /verify by any third party with the public key. This is the artifact regulators, plaintiffs counsel, and D&O carriers ask for.