SRE-IR vs cyber-IR side-by-side
| Capability | SRE-IR (PagerDuty, incident.io, FireHydrant) | Cyber-IR (IR-OS) |
|---|---|---|
| Primary goal | Restore service | Defensible response |
| Audience | On-call engineer, SRE manager | CISO, GC, CFO, board observer, counsel |
| Regulatory clocks | Not in product | GDPR, HIPAA, SEC 1.05, NY DFS, NIS2, DORA, state laws, carrier first-notice |
| Privilege model | Not in product | Channel-scoped, org-level, counsel of record |
| Defensible record | Activity log | SHA-256 hash chain, Ed25519-signed at closure, third-party verifiable |
| Crisis communications | Status page | Stakeholder map, holding-statement library, sign-off trail |
| Panel firms | Not in product | Counsel, forensics, PR, notification vendor, surfaced in workflow |
| Cyber insurance | Not in product | Policy clause as computable entity, first-notice clock |
| Tabletop and AAR | Postmortem template | Cyber scenario library, 8-section AAR scoped to cyber lessons |
What incident response software for security teams looks like
Cyber-specific scenarios
Ransomware, BEC, exfiltration, insider, supply chain, cloud compromise, data breach. Conditional runbooks with branches captured in the record.
Regulatory clock library
Each clock starts from its own trigger. Materiality determination starts SEC 1.05. Becoming aware starts GDPR. Discovery starts HIPAA. Each captured separately.
Counsel-shaped workflow
Privilege chain at the org level by counsel of record. Drafts under privilege until approved. Survives discovery.
Carrier-shaped first-notice
Cyber insurance policy clauses encoded as computable entities. First-notice clock starts on the policy-defined trigger, not on detection.
Board-shaped briefings
Board-observer role with read-only access. Plain-language briefing. Materiality inputs visible. Privileged drafts hidden.
Hash-chained record
Append-only event ledger, SHA-256 chained, Ed25519-signed at closure, third-party verifiable at /verify. Stands up to regulator and shareholder discovery.
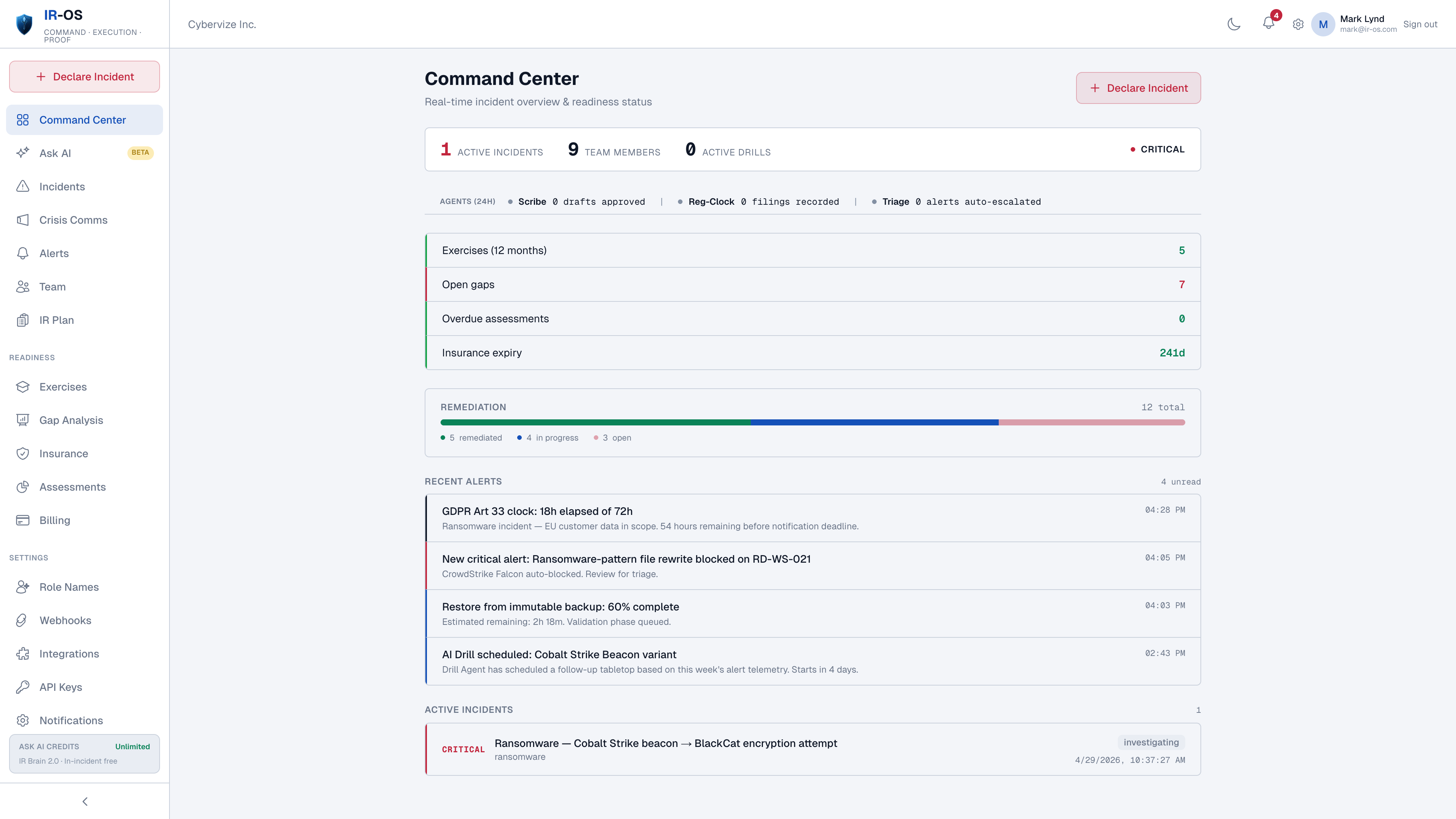
The coexistence pattern
The right division of labor is straightforward. Most security teams will run multiple tools indefinitely. The SRE-IR tool stays for production paging. The ITSM tool stays for engineering remediation. IR-OS owns the cyber-IR command surface during the incident: classify the alert as security-flavored, declare the cyber incident, run the response, produce the record, hand the remediation items to ITSM after AAR. Webhooks connect the layers. Different categories, complementary tools.
Common questions
Is incident response software the same as PagerDuty or FireHydrant?
No. PagerDuty, incident.io, and FireHydrant are SRE incident response - paging an on-call engineer when production breaks. Cyber incident response is a different category: regulatory clocks, breach counsel, structural privilege, hash-chained record, cyber insurance first-notice, panel firms. Those are not SRE features and they are not on the SRE-IR roadmap. Different categories, different tools, can run side by side.
Why does cyber-IR need its own software?
Because the artifacts are different. SRE-IR optimizes for time-to-restore-service. Cyber-IR optimizes for defensible response under regulatory and litigation pressure. The deliverables - 8-K, GDPR Article 33 notice, carrier first-notice, AAR, hash-chained ledger - are not produced by an SRE-IR tool. Forcing cyber-IR through an SRE-IR tool is the most common reason teams cannot answer a regulator inquiry on Day 90.
Does this replace ITSM (Jira, ServiceNow)?
No. ITSM tracks remediation work that comes out of an incident. IR-OS owns the cyber-IR command surface during the incident and produces the defensible record. Remediation items flow from the IR-OS AAR into the engineering or IT backlog where they are worked. The two are complementary.
What does the 7-day free trial include?
Every feature, 25 users, full access to the IR plan generator, runbooks, crisis communications, regulatory clocks, AAR, and the hash chain. Card is required to start the trial; the 30-day money-back guarantee covers any reason. After trial, plans are Squad ($199/mo), Command ($499/mo), and Theater ($799/mo).
Can our team use this without security expertise on every role?
Yes. The defaults reflect what 150+ real C-Suite tabletops show works. The IR plan generator runs a 15-minute conversational interview and produces a customized plan. The IRC role recommender suggests which job title in a typical organization owns each function. Ask AI is citation-grounded so non-expert users can verify guidance before acting. Power users can customize anything.