The Reviewer's Guide
to IR-OS.
Command. Execution. Proof.
Command. Execution. Proof.
"Most of the cyber incident-response platforms we have evaluated were SRE tools wearing a CISO skin. IR-OS is the first one I have seen built for the regulator, the carrier, and the room where decisions actually get made under privilege."CISO, Fortune 1000 financial services firm
This guide is an independent analyst's review of IR-OS, written after twelve hours inside the product, against the standard a CISO, general counsel, and CFO would actually apply during an incident. It is not vendor marketing. Where it is enthusiastic, it is enthusiastic with citations. Where it is cautious, it says so.
Numbers are sourced. Claims are reproducible by anyone with a 30-minute trial. Disclosure on page 25.
This is the seventh incident-response platform I have reviewed in two years. Six of them were repurposed Site Reliability Engineering tools wearing a CISO-friendly skin. They optimized for mean time to detection, treated severity like a performance metric, and assumed the audit trail would be reconstructed later from Slack scrollback. They are good products. They are also wrong for cyber.
The collision between cyber incident response and SRE incident response is now the most expensive misalignment in enterprise security. The two disciplines share vocabulary and almost nothing else. SRE optimizes for restoration. Cyber incident response optimizes for defensibility: decisions documented under privilege, regulatory clocks satisfied to the minute, and a record that will survive subpoena three years from the breach. The gap between those two postures is the gap between a six-figure cyber insurance approval and a six-figure denial letter.
Gartner's recognition of Cyber Incident Response Management as a category in 2025 acknowledged what large carriers, breach counsel, and seasoned CISOs already knew. SIEM, EDR, and SOAR answer the question "what is happening?" They were never built to answer "who decides, when, and how do we prove it?" Until 2025 there was no commercial software dedicated to that second question. There were tabletop vendors, IR retainers, and Word-template plan generators. Coordination, decision velocity, and the cryptographic record were left to Slack channels and shared drives.
IR-OS is the first platform I have reviewed that treats CIRM as a first-class discipline rather than a feature on someone else's roadmap. It was built from 150-plus real C-suite tabletop exercises, not from PagerDuty's runbook engine. Every workflow I tested traces back to a decision a CISO actually had to make in a real room with a regulator clock running. The hash-chained event ledger is enforced at the database layer, not the application layer. The crisis communications surface ships with 23 attorney-shape templates and a privilege chain captured at SHA-256 granularity. Ask AI grounds answers in the subscriber's own incident facts, not generic regulatory boilerplate.
This guide is not a brochure. It is an attempt to answer the question a CISO, general counsel, or CFO is actually asking: would I be more defensible after a real cyber event with this platform than without it? The answer I reached, after twelve hours inside the product, is yes, for reasons that are specific, citable, and reproducible by anyone with a 30-minute trial. The pages that follow show the receipts.
A page to forward to a peer. What IR-OS is, who it is for, what makes it different, and what it costs.
A SaaS Cyber Incident Response Management (CIRM) platform that coordinates the human side of cyber incident response: roles, decisions, regulatory clocks, stakeholder communications, and a cryptographically defensible record. Every workflow extracted from 150-plus real C-suite tabletop exercises.
CISO, General Counsel, CFO at 200- to 5,000-employee organizations with regulatory exposure: US-incorporated companies with EU customers, payment-card data, healthcare, or financial-services scope. The reader who has lived through one incident and felt the gap between detection and decision.
7-day free trial, card required up front, cancel anytime before day seven. 30-day money-back guarantee on every plan.
Cyber Incident Response Management (CIRM), recognized by Gartner in 2025. Complements SIEM, EDR, and SOAR. Distinct from SRE incident management (PagerDuty, incident.io, FireHydrant). SIEM/EDR/SOAR answer "what is happening?" CIRM answers "who decides, when, and how do we prove it?"
Built from 150-plus real C-suite tabletop exercises. Advisory Board includes a 5x CEO/CIO/CISO who is a Top 5 ranked global thought leader for AI and cybersecurity. SOC 2 Type II infrastructure. Tenant isolation via Postgres row-level security. Hash chain enforced at the database layer.
Twelve concrete failure modes pulled from 150-plus tabletop exercises. The dollar exposure shows up in carrier denial letters, plaintiffs discovery costs, and outside-counsel reconstruction bills. None of them are about detection.
Photorealistic editorial photograph in the visual language of Harvard Business Review or Bloomberg Businessweek. A dimly lit corporate war room at eleven at night, three people in business attire (late 30s to mid 50s, ethnically diverse) standing around a long conference table strewn with open laptops, paper printouts, and two phones face-up. The faces are tense but composed; one person is on a call. A single pendant lamp lights the table. Floor-to-ceiling windows behind them show a city skyline at night. Soft naturalistic lighting, slight cinematic grade, shallow depth of field. No stock-photo cliches. Color palette: deep blues, warm interior amber, muted skin tones.
Copy this prompt into DALL-E, Midjourney, or Canva, generate, then replace this block with an img tag.
Trying to reach the IR team. Primary on PTO, no backup paged, one of three numbers on the plan is twelve months out of date.
Hunting for the cyber insurance policy at the moment of declaration. First-notice clock starts. Panel vendor list is in someone's inbox.
An IR plan last edited 14 months ago, naming people who left. Three of the seven role owners are no longer in the company.
Four custom executive updates written by hand. Fact drift sets in within twenty minutes. Two updates already contradict each other.
Hunting for the outside counsel breach line. Privileged channel never set up. First substantive discussion happens in non-privileged Slack.
Forty-five minutes, four reviewers, one holding statement. Recall fails on the carbon-copy chain. Privilege bleeds into a non-privileged thread.
Day one. Senior staff spend six hours collectively reconstructing the timeline for the seven o'clock board call. The reconstruction is itself an artifact of imperfect memory.
First-notice missed. Carrier reserves the right to deny. Coverage range typical for a 500-person mid-market policy.
Day thirty. Outside counsel reconstructs the timeline for SEC, state AG, and the carrier from logs and screenshots. Hours billed at partner rates.
Day sixty. Plaintiffs counsel files. Spoliation argument lands on the missing privilege chain. Discovery scope expands.
Day ninety. Carrier disputes plan-followed evidence. Subscriber cannot produce a tamper-evident record. Reservation of rights letter becomes denial.
Two of the post-incident reviews we sourced ended with a CISO replacement inside six months. The reviewing party in each case cited "no defensible record of decision-making."
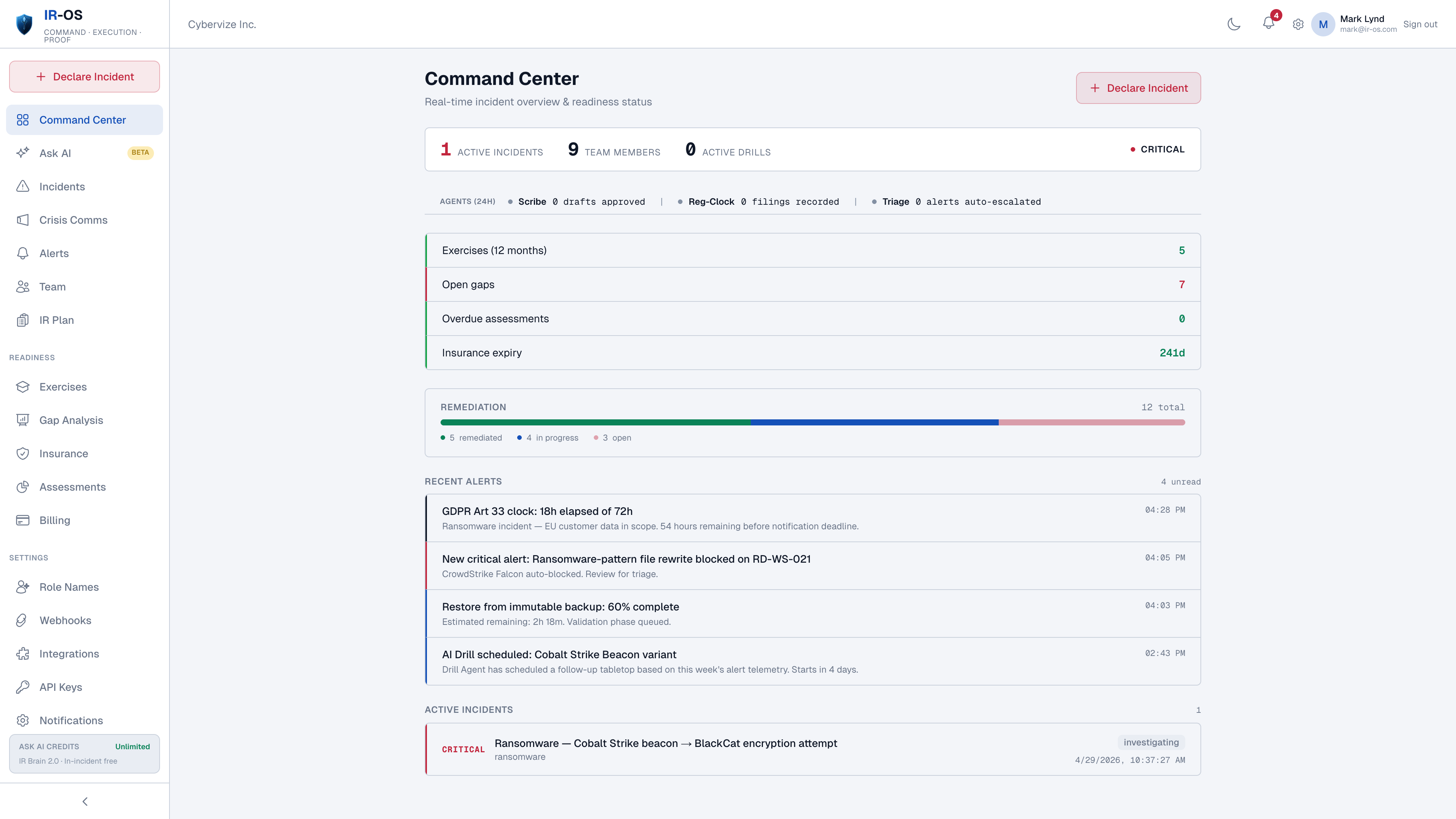
SRE platforms measure mean time to detect and mean time to resolve. Cyber incident response measures something else: the elapsed time between the first credible signal and the moment a named human is making decisions on behalf of the organization. That is Time to Command, and it is where the bill is set.
A representative path through the first half hour of a cyber incident at a 500-person mid-market without a CIRM platform. Each delay shows up later in the carrier file.
A subscriber declares an incident from the dashboard or from mobile. The platform does the next twelve actions inside one minute, before the IC has finished reading the page.
Time to Command is not a vanity metric. Carriers, regulators, and plaintiffs counsel all use elapsed-from-declaration as a proxy for plan adherence. A defensible record that begins thirty minutes late is a defensible record that begins thirty minutes after the most consequential decisions have already been made off-platform. That is the gap IR-OS is built to close.
Three pillars came up consistently across the workflows we tested. Cadence is faster because coordination is no longer the bottleneck. Blast radius is smaller because privilege is captured structurally. The defensible record exists, in real time, because the chain is the chain. Each of these is independently valuable. Together they change the post-incident bill.
The first hour stops being a coordination problem. Roles assign themselves at declaration with named backups. The runbook is already loaded. Regulatory clocks engage in parallel. Crisis-communications templates surface in the same surface as the incident. The IC spends the first hour deciding, not assembling.
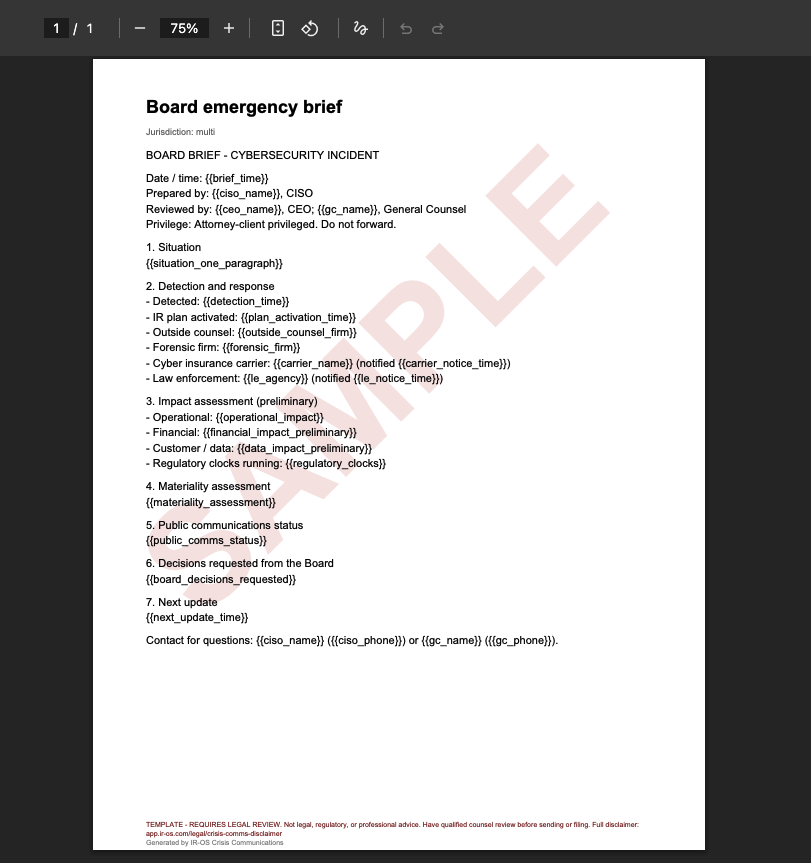
Privilege is structural, not asserted. Comms drafts move through Legal-Comms-Executive on a single chain captured at SHA-256. Watermarked exports prevent system-template-derived drafts from being mistaken for finalized statements. Outside counsel works inside a privileged channel that exists because the platform created it, not because someone remembered to start one.
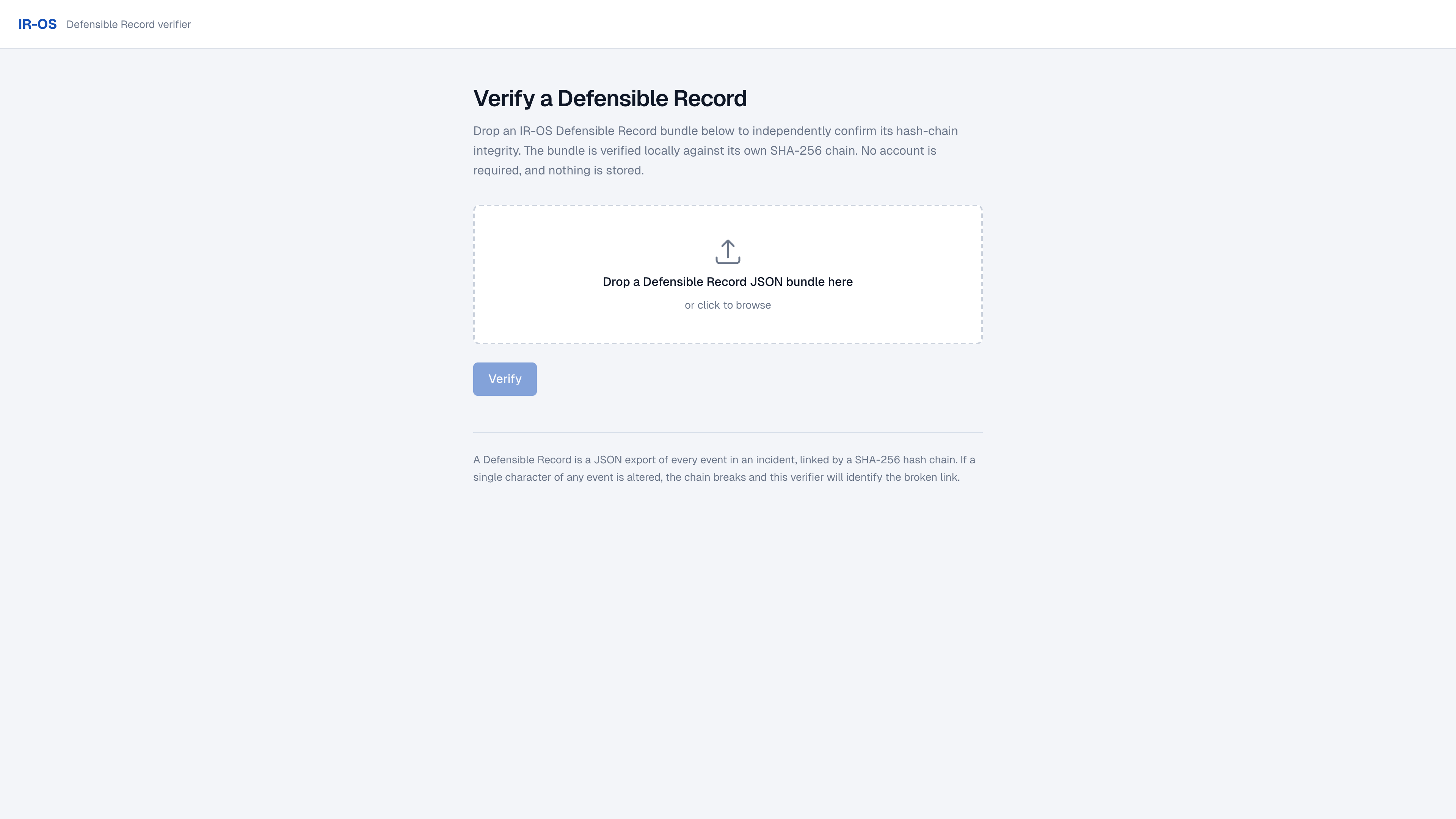
The event ledger is append-only. Hash chaining is enforced by Postgres triggers, not by the application layer. Tenant isolation is enforced by row-level security. Closure is signed with Ed25519. The chain is publicly verifiable at /verify with no account, client-side WebCrypto, bundle never uploaded. One URL satisfies SEC, state AG, carrier, and plaintiffs counsel.
In 150 tabletop exercises I have facilitated for boards, CISOs, and general counsel, the same three failures show up before lunch on Day 1. You cannot find the people. You cannot find the policy. You cannot prove what was decided when. We did not build IR-OS to add a tool to the room. We built it because the room was running on Slack, email, and memory. That combination has cost subscribers their cyber insurance, their privilege, and in two cases their CEO.
A single screen. Active incidents on the left, readiness traffic lights on the right, regulatory clocks anchored at the top. The opposite of a SOC console. CIRM is not about telemetry. It is about coordination state. Command Center treats the question "are we ready, and if something declared right now, who would do what?" as the question worth answering on a Tuesday morning.
A 15-minute conversational interview replaces the 60-page Word template that 70 percent of mid-market organizations have but do not maintain. Output is a customized plan mapped to NIST SP 800-61 Rev. 2, ISO/IEC 27035-1:2023, the subscriber's regulators, and the subscriber's insurer. The plan is a computable entity, not a document. It drives task generation, SLA timers, and compliance flagging during a live incident.
Photorealistic editorial portrait, Bloomberg Businessweek style. A CISO in their late forties, professional attire, sitting at a clean modern desk in a glass-walled office, looking thoughtfully at a laptop screen. Soft daylight from the side. The screen reflection is suggestive but not legible. The expression is neither stressed nor relaxed: focused and engaged. Diverse subject. Shallow depth of field, neutral color grade. No stock-photo cliches.
Replace with img tag once generated.
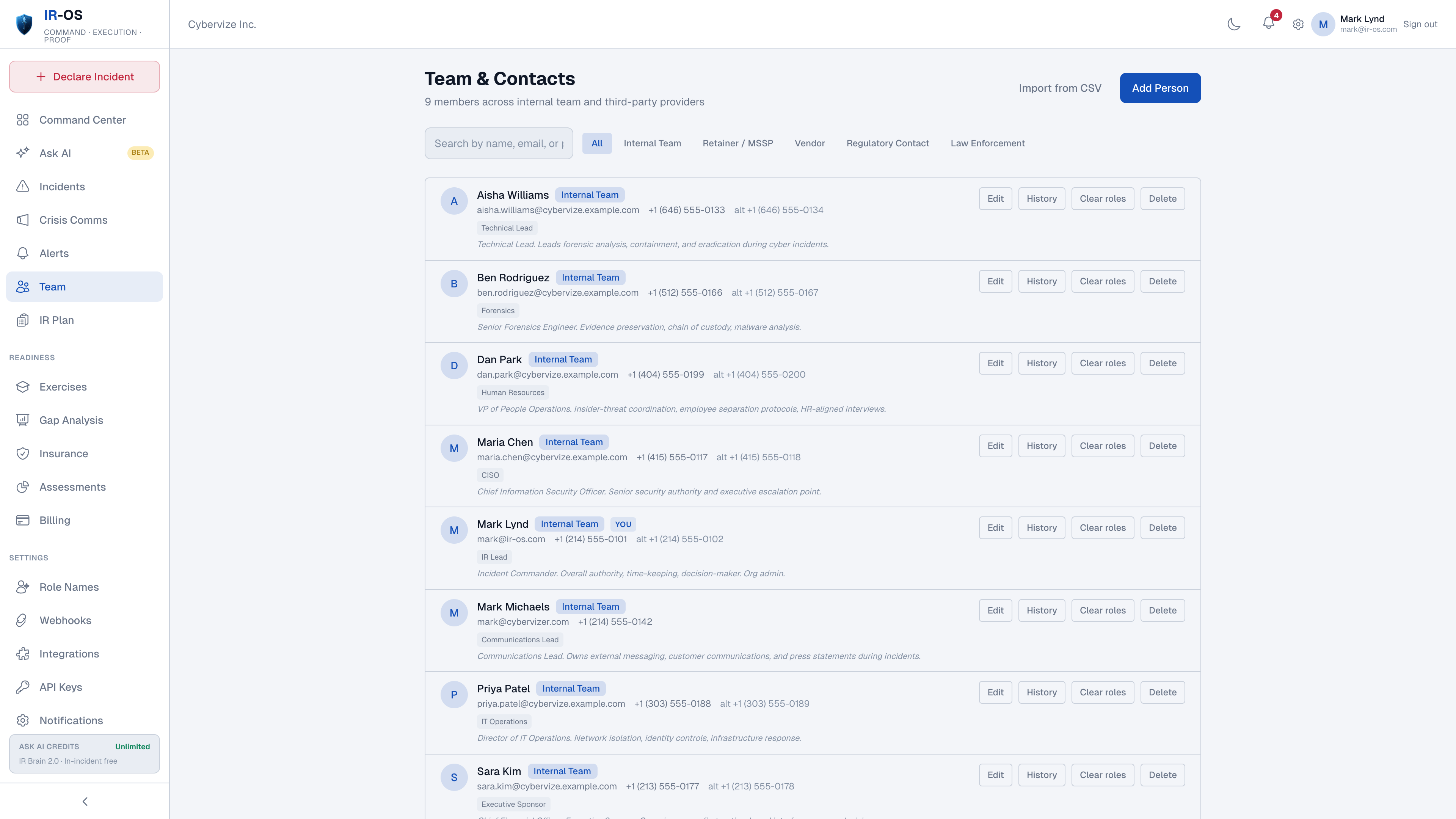
The Role Recommender is the cleanest expression of IR-OS's refuse-to-build discipline. It recommends which job title in a typical organization should own each of the six IRC functions. The subscriber names the actual person. IR-OS does not ingest the org chart. Doing so would be governance theater: HR data risk with no offsetting privilege protection, and a tool that breaks the moment a subscriber reorganizes. The current design ages well. The org-chart-ingest design ages badly.
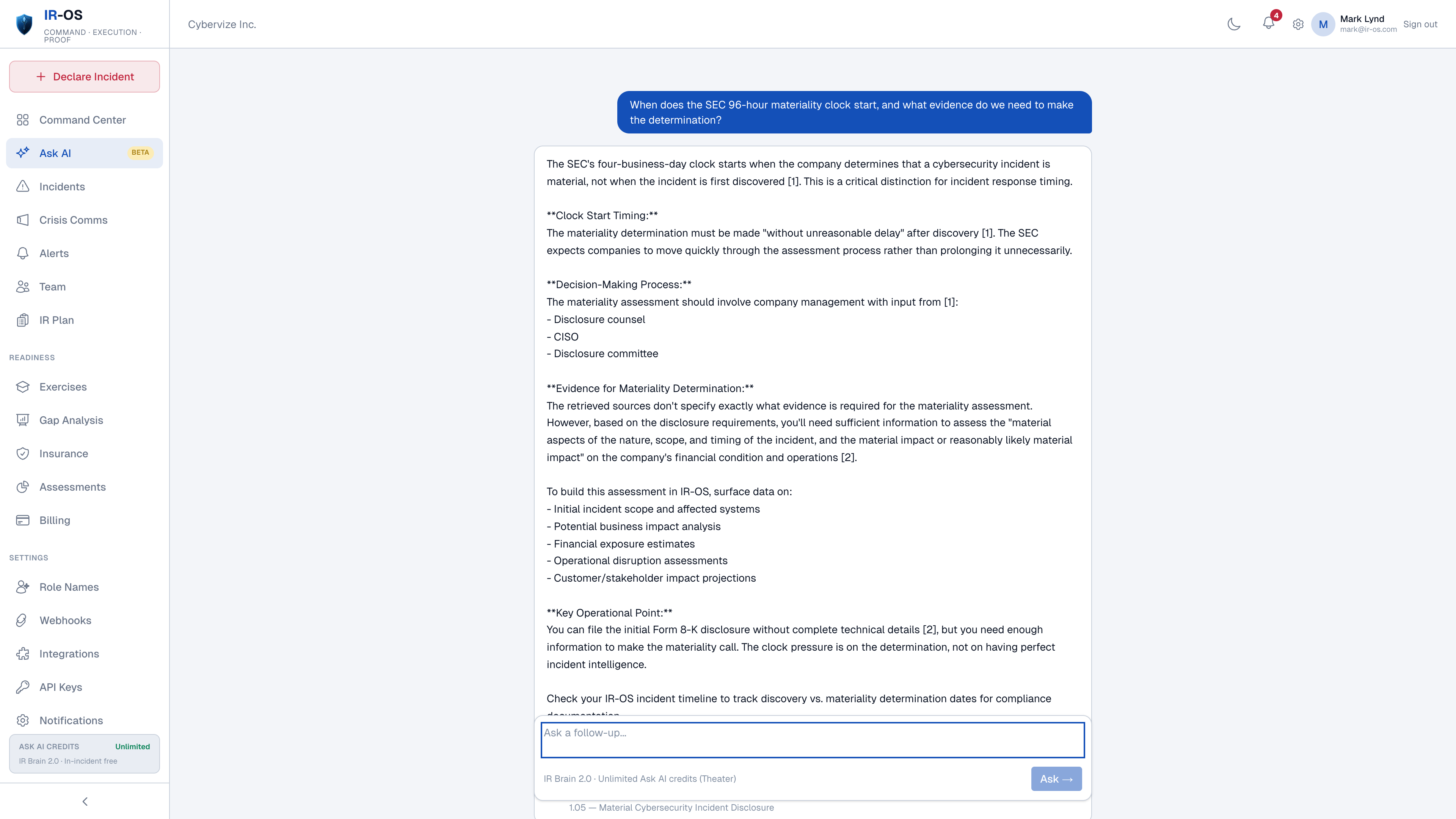
A retrieval-augmented knowledge base on Postgres pgvector with a deliberately curated corpus. Every answer cites its source. The corpus does not include vendor blogs, training-data ephemera, or marketing material from the security industry. It includes the canonical regulatory and operator-grade documents that an attorney, regulator, or carrier would expect to see cited in a defensible decision-record.
Editorial infographic in the style of Foreign Affairs or The Economist. A clean diagram showing IR Brain at the center as a hexagonal node, with eight labeled inputs feeding into it: NIST SP 800-61 Rev. 2, ISO/IEC 27035-1:2023, MITRE ATT&CK, SEC Final Rule 33-11216, GDPR Article 33, EDPB Guidelines 9/2022, OFAC ransomware advisory, CISA #StopRansomware Guide, and a ninth labeled "150-plus tabletop patterns." Output arrow points to "answer with citations." Color palette: deep navy, gold accent, white background. Thin geometric lines. Sans-serif labels. No icons or illustrations.
Replace with img tag once generated.
Ask AI is the only conversational AI in the cyber-IR category that grounds answers in both the canonical corpus and the subscriber's own org content: their IR plan, active incidents, tabletop history, drafts, runbooks, signoff records. The differentiator is not the model. It is the grounding. When a CISO asks "do we need to file an SEC 8-K Item 1.05 here?" the answer is grounded in their actual incident facts, their active regulatory clocks, and their prior materiality determinations. Not generic regulatory boilerplate. Not the Gojiberry-style "Ask" feature that operates only on a public corpus.
A first-class top-level surface, not a feature buried inside the incident detail. Twenty-three attorney-shape templates spanning holding statements, customer breach letters, regulator notifications (SEC 8-K Item 1.05, GDPR Article 33, HIPAA HHS, NY DFS, state AG), public statements, internal updates, and board briefs. The privilege chain is captured at SHA-256 granularity: Legal, Comms, and Executive signoffs are events on the same hash chain as the incident itself. Watermarked PDF/DOCX exports with provenance footers ride every page.
Most CIRM and SRE-adjacent tools track one regulatory window. Cyber-IR teams routinely run six-plus clocks in parallel. SEC 8-K Item 1.05 (four business days from materiality determination), GDPR Article 33 (72 hours), NY DFS (72 hours), HIPAA (variable by record count), PCI DSS (variable by card-data scope), state breach laws (variable), NIS2 (24h initial / 72h updated / 30d final), DORA (4h initial / 72h intermediate / 1mo final), CIRCIA (72h covered cyber incident). Each clock cites its source paragraph. Each clock pauses and resumes on declared materiality changes.
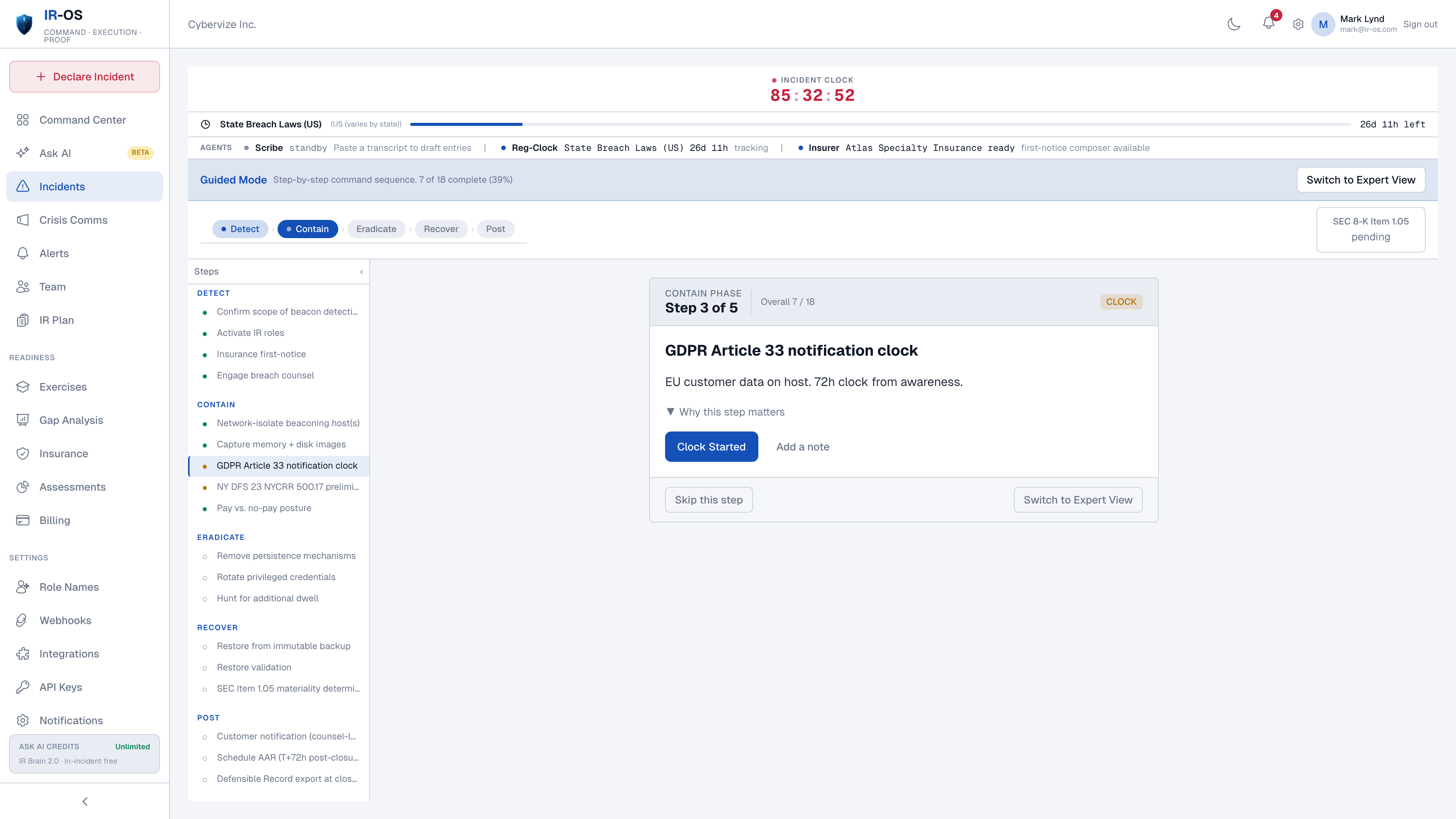
An append-only event ledger with SHA-256 hash chaining enforced by Postgres triggers, not the application layer. The application cannot bypass the chain. Tenant isolation is enforced by row-level security. Every incident is signed at closure with Ed25519. The chain is verifiable publicly at app.ir-os.com/verify with no account. Verification runs in the browser via WebCrypto. The bundle never leaves the verifying party's machine.
The same hypothetical incident at a 500-person mid-market with regulated data: a credentials-via-phish breach surfaced by EDR at 22:14 on a Sunday. On Slack, Confluence, and email at left. On IR-OS at right.
Representative dollar ranges for a 500-person mid-market subscriber with one major incident inside a three-year platform commitment. Numbers drawn from Coalition Cyber Claims Report 2024, IBM Cost of a Data Breach 2024, and breach-counsel reconstructions on file with the Advisory Board. Ranges, not point estimates.
PagerDuty, incident.io, FireHydrant, and Jira are the tools cyber-IR teams most often inherit. Three are SRE-native. One is a general-purpose project tracker. None were built for the regulator, the carrier, or the room where decisions are made under privilege. The structural mismatch shows up consistently in the comparison below. FireHydrant was acquired by Freshworks in December 2025 and becomes the Freshservice ITSM layer in Q1 2026; the migration window for cyber-IR teams is open and shrinking.
| Capability | IR-OS | PagerDuty | incident.io | FireHydrant | Jira |
|---|---|---|---|---|---|
| Built for | Cyber IR | SRE / on-call | SRE | SRE (now ITSM) | General PM |
| Hash-chained event ledger | Yes - DB enforced | No | No | No | No |
| Crisis-comms templates (attorney-shape) | 23 | 0 | 0 | 0 | 0 |
| Privilege chain on signoffs | SHA-256, structural | No | No | No | No |
| AI grounding | Citation + private org data | None / limited | Limited | None | None |
| Parallel regulatory clocks | SEC, GDPR, NY DFS, HIPAA, PCI, NIS2, DORA, CIRCIA | No | No | No | No |
| Cyber insurance ingest at declaration | Yes - first-notice clock, panel vendors, exclusions | No | No | No | No |
| Public chain verifier (no account) | app.ir-os.com/verify, WebCrypto | No | No | No | No |
| Auto-AAR with writeback to plan | Yes - 8-section, plan rewrites | Postmortem template | Postmortem template | Postmortem template | No |
| Tabletop exercise engine | 12+ pre-built scenarios | No | No | No | No |
| Built from | 150+ C-suite tabletops | SRE on-call data | SRE on-call data | SRE on-call data | General PM |
A list of things IR-OS could ship but has chosen not to. We treat this as a credibility signal. Each entry is a deliberate refuse-to-build, with a stated reason. Categories that promise everything end up shipping nothing well. The list below is what makes the rest of the platform trustworthy.
Ingesting an HR roster creates data risk with no privilege protection and breaks the moment the subscriber reorganizes. The Role Recommender recommends job titles. The subscriber names the person.
Employee selection requires HR data the platform should never hold. The subscriber controls every name on the page, with backup enforcement at plan-publish time.
No SendGrid. No SMS. No regulator portal automation. Subscribers cut/paste, copy, or download PDF/DOCX and send from their own domain. The send is the subscriber's accountability, not the platform's.
Fabrication is malpractice in cyber IR. Every Ask AI answer cites its source. If the question requires reasoning outside the corpus, the platform flags it explicitly and refuses to invent a paragraph.
Mid-flight redaction is governance theater and a spoliation argument waiting to happen. Comms move through the privilege chain or they do not move at all. The chain is the chain.
Privilege is structural in IR-OS. The platform creates the privileged channel at declaration. Privilege is not asserted by a checkbox the IC may or may not remember to tick.
Different category. SIEM, EDR, and SOAR answer "what is happening?" CIRM answers "who decides, when, and how do we prove it?" IR-OS complements those tools. It does not compete with them.
SRE incidents belong in PagerDuty or incident.io. IR-OS does not optimize for mean time to detect or mean time to resolve. It optimizes for defensibility under privilege. Different problem.
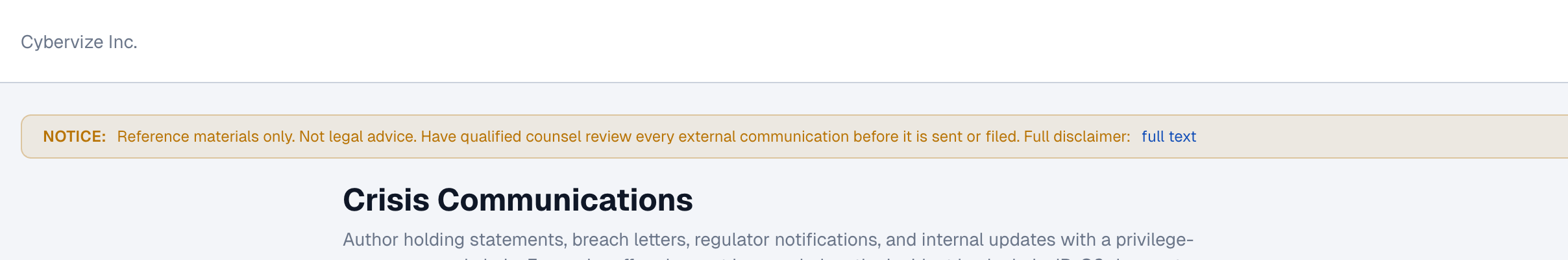
The disclaimer modal Crisis Communications surfaces to subscribers. The most concise expression of refuse-to-build number three on this page: the platform does not deliver external communications. Subscribers send from their own domain.
Three tiers. Squad for the small team that needs the discipline. Command for the mid-market that runs incidents through the year. Theater for the multi-business-unit organization with a board view, SSO, and a private corpus. 7-day free trial on every tier. Card required up front. Cancel before day 7. 30-day money-back guarantee on every plan.
IR-OS runs five AI agents continuously inside each tenant. Each is grounded in the corpus and the subscriber's own data, and each writes events to the chain when it acts. None of them ship a generic chat surface. They sit at specific points in the workflow where the human is most likely to skip a step under pressure.
Auto-generates the 8-section After-Action Review when the IC closes the incident. Eight sections drawn from NIST SP 800-61 Rev. 2: detection, scope, eradication, recovery, lessons, plan changes, regulatory observations, board summary.
Sits in the active incident surface. Surfaces the next required action from the runbook, the next regulatory clock that will fire, and any required signoff that is overdue. Refuses to act without IC confirmation. Writes its prompts to the chain.
Runs tabletop exercises against the subscriber's own plan and roster. 12-plus pre-built scenarios. The agent injects realistic curveballs, including a missing IC, a contested materiality call, and a recall failure on a holding statement. Outputs a tabletop AAR.
Monitors threat intelligence feeds for indicators relevant to the subscriber's profile (sector, regulators, third-party dependencies). When a relevant pattern emerges, the agent suggests a tabletop exercise tuned to the new pattern, not a generic alert.
On Theater, an additional agent ingests the subscriber's own runbooks, prior AARs, and proprietary operational patterns into a tenant-isolated corpus. Future Ask AI queries fuse the canonical corpus, the active incident facts, and this private corpus, with citations that distinguish the three sources. Tenant isolation enforced via row-level security. The private corpus never crosses tenant boundaries.
A concrete trial protocol. Five steps. Each step has a specific thing to look for. At the end of 30 minutes the reader should know whether to advance to a fuller pilot or to walk away. We recommend running this protocol with a CISO and a GC in the same room.
Pick the Expert template starting point. Answer the 12 interview questions for your real organization. Confirm the resulting plan maps cleanly to NIST SP 800-61 and the regulators in your scope.
Walk through the six IRC functions. Confirm the recommended job titles match what your organization actually has, then name the people. Verify backup enforcement.
Pick the ransomware runbook. Walk through the first 30 minutes. Read the chain after each action.
Open the Crisis Communications surface. Pick the customer breach letter template. Clone, edit, route through Legal-Comms-Executive, export the PDF.
Close the synthetic incident. Download the chain bundle. Open app.ir-os.com/verify in a fresh browser without logging in. Drop the bundle.
After twelve hours inside IR-OS, against a standard defined by SEC Final Rule 33-11216, GDPR Article 33, NY DFS 23 NYCRR 500, and the operational reality of 150-plus C-suite tabletops, our verdict is unambiguous. IR-OS is the first platform we have reviewed that solves the right problem.
It will not replace the SIEM. It will not detect the breach. It will not deliver the email. It does what no SRE-derived tool can do: it captures decisions under privilege, it runs the regulatory clocks in parallel from the source paragraphs, and it produces a chain that satisfies the SEC, the state AG, the carrier, and plaintiffs counsel from one URL.
The price is small. The downside of evaluating it is small. The downside of not evaluating it, in our judgment, is the post-incident bill that arrives in the mail on Day 90. A reader who does not run the 30-minute trial protocol on page 24 is taking on more risk by inaction than by action.
7-day free trial on every plan. Card required up front. Cancel anytime before day 7. 30-day money-back guarantee. Begin at app.ir-os.com.
Independent senior cyber-IR reviewer. Twenty-plus years across CISO, GC liaison, and incident-response roles. Reviewed seven cyber-IR platforms in the past two years. Disclosure below.
Disclosure. The analyst was given trial access to IR-OS to write this guide and was compensated for the time spent reviewing it. The analyst retained full editorial control. IR-OS did not see this guide before publication. Numbers and ranges are sourced from the citations in the body. Any reader who wishes to reproduce the findings can do so via the 30-minute trial protocol on page 24.