What cyber incident management owns
Human coordination
Six pre-defined IRC roles. Single owner per task. Explicit handoffs. State + Role = View. Show only valid next actions.
Regulatory clocks
GDPR, HIPAA, SEC Item 1.05, NY DFS, NIS2, DORA, state breach laws, cyber insurance first-notice. Each from its own start event.
Structural privilege
Channel-scoped attorney-client privilege at the org level by counsel of record. Drafts under privilege. Survives discovery.
Crisis communications
Stakeholder map, holding-statement library, sign-off trail. Watermarked SAMPLE exports for tabletop. Privileged drafts under counsel review.
Defensible record
Append-only event ledger, SHA-256 chained, Ed25519-signed at closure, third-party verifiable at /verify.
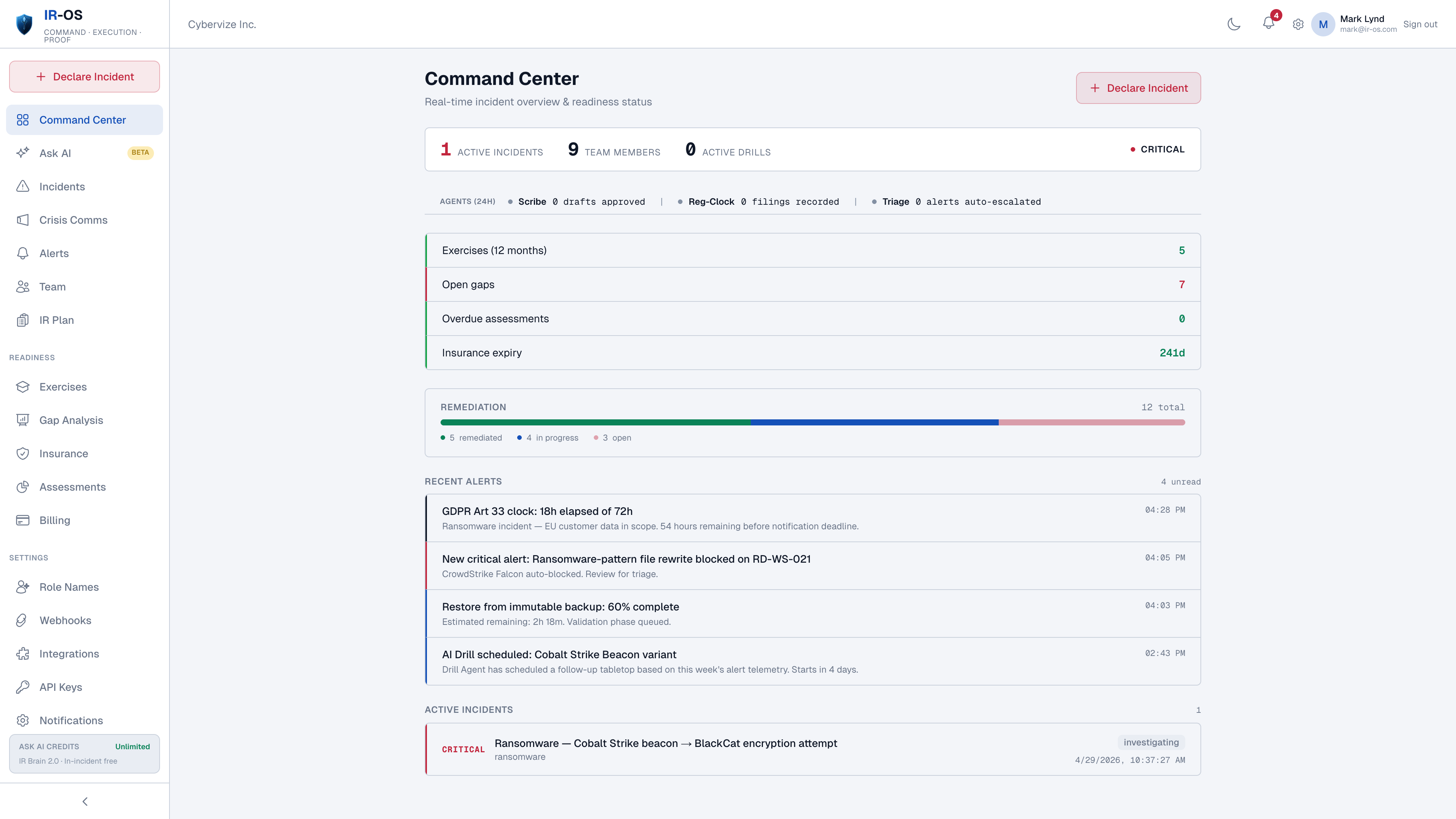
Readiness loop
Tabletop scenarios, IR plan as computable entity, gap remediation tracker, readiness traffic lights. Same workflow as response, on a different timeline.
Why CIRM exists as a category
SIEM was solved. EDR was solved. SOAR was solved. The thing that kept causing breaches to escalate from operational to existential was not detection - it was the next eight hours after the alert. Who declares the incident. Who runs the clock. Who calls counsel. Who signs the holding statement. Whether the carrier first-notice fired in the policy window. Whether the record is going to survive a regulator inquiry on Day 90. None of those questions are answered by SIEM, EDR, or SOAR; they are not what those tools are for. CIRM is the category that answers them, and IR-OS is built specifically for the cyber-IR coordination problem.
Who uses a cyber incident management platform
The audiences a cyber incident actually has. CISOs, IR leads, General Counsel, communications leads, CFOs, board observers, outside counsel of record. Not on-call engineers - that audience uses SRE-IR tools (PagerDuty, FireHydrant, incident.io). Not the IT service desk - that audience uses ITSM (Jira, ServiceNow). CIRM sits next to those tools, owns the cyber-IR command surface, and produces the artifacts the cyber audience needs.
Common questions
What is cyber incident management?
Cyber incident management (CIRM, Cyber Incident Response Management) is the Gartner-recognized category that solves the human side of incident response: coordination, decision velocity, regulatory clocks, structural privilege, crisis communications, and the defensible record. CIRM complements SIEM (detection), EDR (endpoint response), and SOAR (technical automation). Where those solve technical workflows, CIRM solves human coordination, the regulator-facing artifact, and the legal-facing record.
How does CIRM differ from SOAR?
SOAR automates technical playbooks against systems: isolate the host, block the indicator, pull forensics. CIRM coordinates humans against decisions: declare the incident, name the IRC, start the GDPR Article 33 clock, draft the 8-K, get counsel sign-off, file carrier first-notice. The two layers run side-by-side. SOAR keeps automating; CIRM keeps coordinating; webhooks connect them.
Who uses cyber incident management software?
CISOs, IR leads, General Counsel, communications leads, CFOs, board observers, and outside counsel. The audiences a cyber incident actually has, in the roles each plays during an incident. Not on-call engineers - that audience uses SRE-IR tools (PagerDuty, FireHydrant, incident.io).
What is the defensible record and why does it matter?
The defensible record is an append-only, SHA-256 hash-chained, Ed25519-signed event ledger covering the full incident lifecycle - decisions, determinations, regulator submissions, carrier first-notice, panel-firm engagements, AAR. Third-party verifiable at /verify. It matters because on Day 90 the regulator, plaintiffs counsel, or D&O carrier wants to see the timeline and process you actually ran. The record answers their questions before they have to ask.
How does cyber incident management connect to readiness?
Readiness is the input to incident management. Tabletop exercises, IR plan, IRC roles, gap remediation, and the readiness traffic lights are not separate from incident response - they are the same workflow on a different timeline. IR-OS treats the IR plan as a computable entity that drives task generation, SLA timers, and compliance flagging during the incident, then captures gaps from the AAR back into the readiness loop.