What the platform does on Day 1
Declare and classify
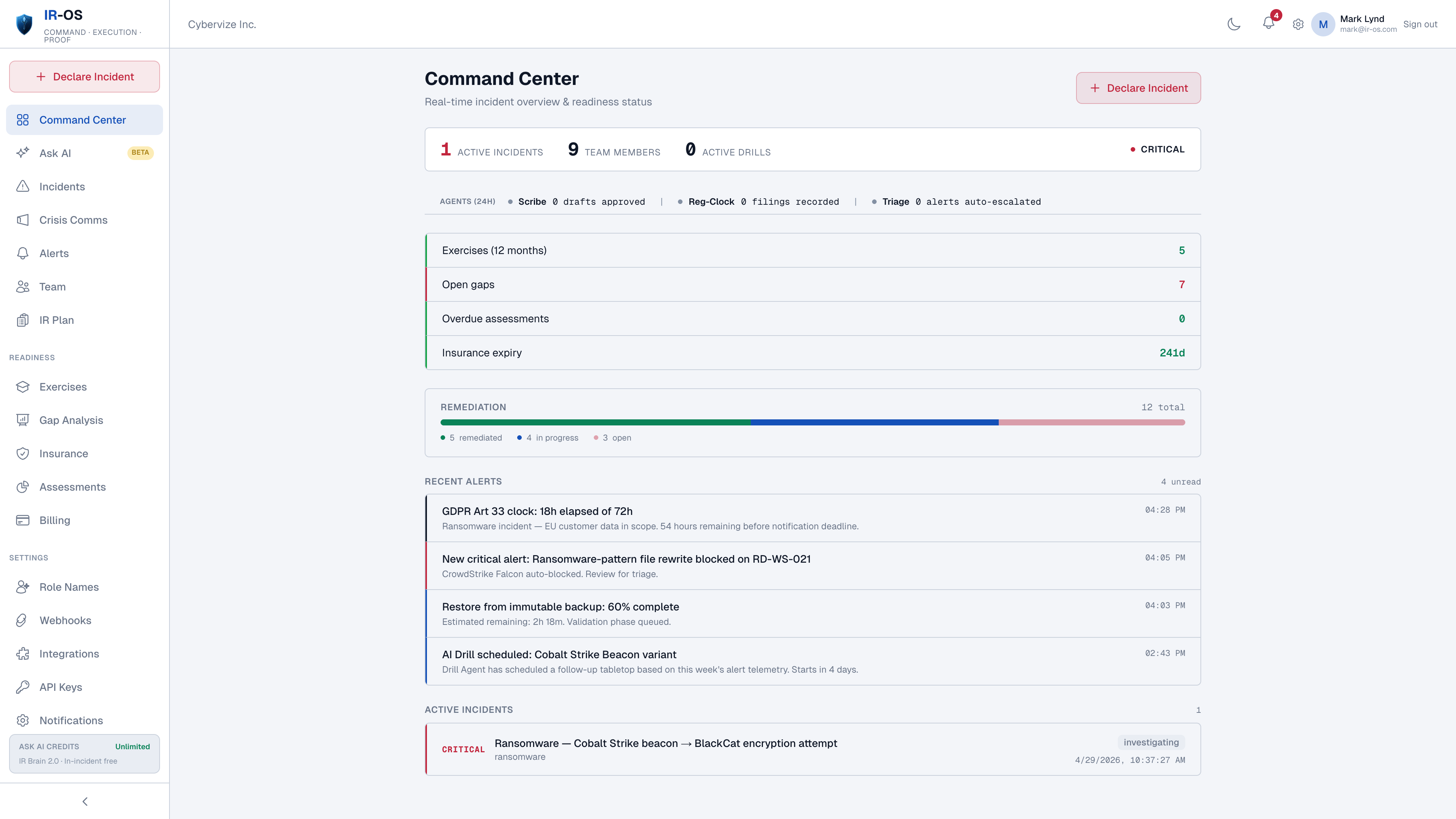
Webhook ingestion from PagerDuty, incident.io, generic SIEM/EDR/SOAR. Security-classification edge fires the cyber incident with the full command surface engaged.
Name the IRC
Six pre-defined roles with two named backups each. State + Role = View. First-time users get a working response without reading the manual.
Run the scenario runbook
Conditional branches captured in the record. Path taken visible in the AAR. Cyber-shaped scenarios, not generic SRE templates.
Start the clocks
GDPR Article 33, HIPAA, SEC Item 1.05, NY DFS, NIS2, DORA, state breach laws, cyber insurance first-notice. Each from its own start event.
Hold the privilege
Channel-scoped attorney-client privilege at the org level by counsel of record. Drafts under privilege until counsel approves release.
Write the record
Append-only event ledger, SHA-256 chained, Ed25519-signed at closure, third-party verifiable at /verify.
The platform philosophy
Most cyber-IR platforms are feature catalogs the team has to learn. IR-OS is a default-behavior platform: the runbook fires when the incident is classified, the regulatory clocks start at the right events, the panel firms appear at the right moments, the record writes itself. Power users can override anything; first-time users get a working response without choosing twelve settings under pressure. That default-behavior model is the difference between a platform that helps during an incident and a platform that needs ten hours of pre-incident configuration the team never finishes.
Common questions
What is a cyber incident response platform?
A cyber incident response platform is the software a security team uses to coordinate humans during a cyber incident: declare the incident, name the IRC roles, run scenario runbooks, manage crisis communications under privilege, track parallel regulatory clocks, and produce a defensible record. It complements detection tools (SIEM, EDR, SOAR) which solve technical workflows. The platform owns the human coordination layer and the regulator-facing artifact.
How is this different from a ticketing tool?
Tickets capture work. A cyber incident response platform captures decisions, determinations, regulatory clocks, privilege chain, and a hash-chained record. None of those are ticket-shaped. Ticketing tools were not designed for the cyber-IR command surface; retrofitting them is the most common reason teams cannot answer a regulator inquiry on Day 90.
What is the time-to-value for a new platform?
Five-minute setup yields a working IR plan, default IRC roles, scenario runbooks, parallel regulatory clocks, and the dashboard. The defaults reflect what 150+ real C-Suite tabletops show works. The IR plan generator runs a 15-minute conversational interview that produces a customized plan mapped to NIST 800-61, ISO/IEC 27035, your regulators, and your insurer.
Does the platform integrate with our existing stack?
Yes. Webhook ingestion from PagerDuty, incident.io, generic SIEM/EDR/SOAR via Bearer-token API. Slack and Microsoft Teams integration captures conversation into scoped, privilege-aware channels. SSO via SAML/OIDC. The detection stack keeps detecting; IR-OS owns the coordination layer above it.
Who are the platform users during an incident?
Six pre-defined IRC roles: Incident Commander, Scribe, Communications Lead, Legal Liaison, Technical Lead, Executive Sponsor. Plus a board-observer role for read-only briefings during major incidents. Each role sees a State + Role view that surfaces only valid next actions, so first-time users get a working response without learning the platform under pressure.