Four reporting audiences, one source of truth
Internal escalation
Executive sponsor briefing, structured handoffs between technical, legal, comms, and executive workstreams. Single owner per task. Explicit handoff events written into the ledger.
Regulator notification
GDPR Article 33, HIPAA, SEC Item 1.05, NY DFS 500.17, state AGs, NIS2 SPOC, DORA competent authority. Each on its own clock. Each with a counsel-approved draft.
Cyber insurance first notice
Carrier policy clauses encoded as computable entities. First-notice clock starts on the policy-defined trigger. Late first-notice is the most common cause of voided coverage.
Board and audit committee
Board-observer role with read-only access. Plain-language briefing. Materiality inputs visible. Privileged drafts hidden. Full record exportable for the audit committee.
Privilege chain
Channel-scoped attorney-client privilege at the org level. Drafts under privilege until counsel of record approves release. Survives discovery.
Hash-chained record
Append-only ledger, SHA-256 chained, Ed25519-signed at closure, third-party verifiable at /verify. The artifact every audience asks for.
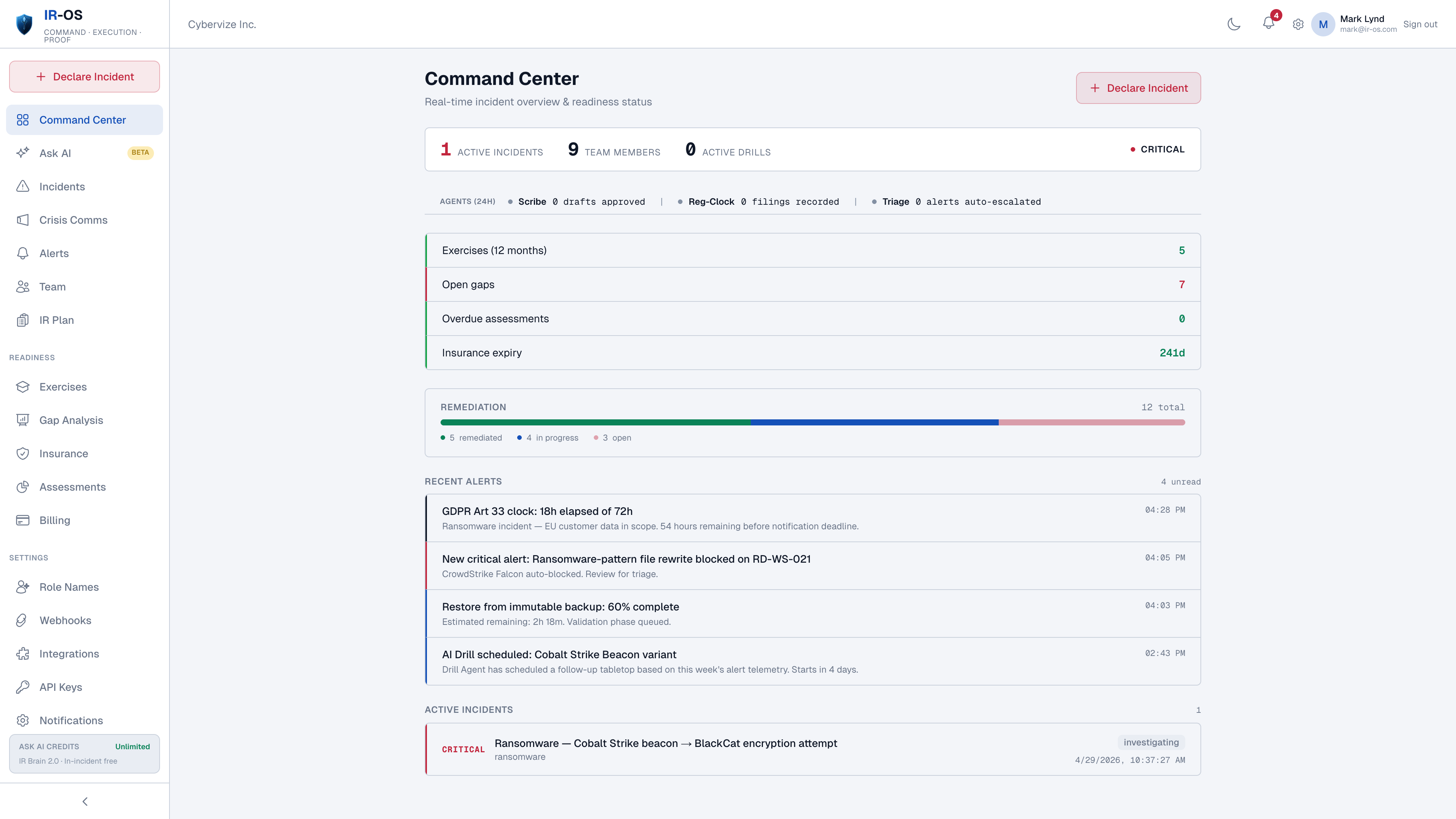
The reporting problem the platform solves
The four audiences want different things and want them at different times. The internal escalation audience wants a one-paragraph summary by the next executive briefing. The regulator wants the determination, the timeline, and the affected population by the clock. The carrier wants first-notice within the policy window or the claim is at risk. The board wants the plain-language briefing 30 minutes before the audit committee meets. None of those four views is producible from a Slack thread, an email chain, or a generic ticket. They are producible - and defensible - from a single incident record with role-scoped lenses and a hash-chained ledger underneath. That record is what IR-OS is.
Common questions
What does cyber incident reporting cover?
Four audiences, four different reports, often at the same time. Internal escalation to executive sponsor and board observer. Regulator notification (GDPR DPA, HHS OCR, SEC, state AGs, NIS2 SPOC, DORA competent authority). Cyber insurance first notice to the carrier. Board and audit committee reporting. IR-OS produces each report from the same source-of-truth incident record, with role-scoped views so each audience sees what is relevant to them.
How is this different from filing a ticket in Jira or ServiceNow?
Tickets capture work. Cyber incident reporting captures decisions, determinations, regulatory clocks, privilege chain, and a hash-chained record. None of those are ticket-shaped. ITSM tools were not designed for the cyber-IR reporting surface; trying to retrofit them is the most common reason teams cannot answer a regulator inquiry on Day 90.
Does the same incident record drive all four reporting audiences?
Yes. One incident record. Role-scoped views. The CISO sees technical scope, the GC sees disclosure drafts and privilege chain, the CFO sees insurance first-notice and materiality inputs, the board observer sees the executive briefing. All four views read from the same hash-chained ledger.
Where does cyber insurance fit?
Carrier first-notice is the most commonly missed clock in cyber-IR. Policy clauses are encoded as computable entities. The carrier first-notice clock starts on the policy-defined trigger and surfaces in the workflow alongside regulatory clocks. Late first-notice is the most common cause of voided coverage; treating it as a peer to GDPR or SEC reporting prevents that.
Can the board see the incident in real time?
Yes, with the board-observer role. Read-only access to the incident dashboard, plain-language briefing summary, regulatory clock status, and material decisions. The board observer does not see privileged drafts. The full record is exportable for the audit committee meeting after closure.