The reporting problem on Day 1
The hard part of SEC reporting is not writing the 8-K. The hard part is making and defending the materiality determination, then proving on Day 30 - in front of an SEC enforcement attorney or shareholder counsel - that you ran the right process at the right time with the right people in the room. Detection logs from the SIEM do not answer that question. Slack threads do not answer that question. A spreadsheet of "decisions made" does not answer that question.
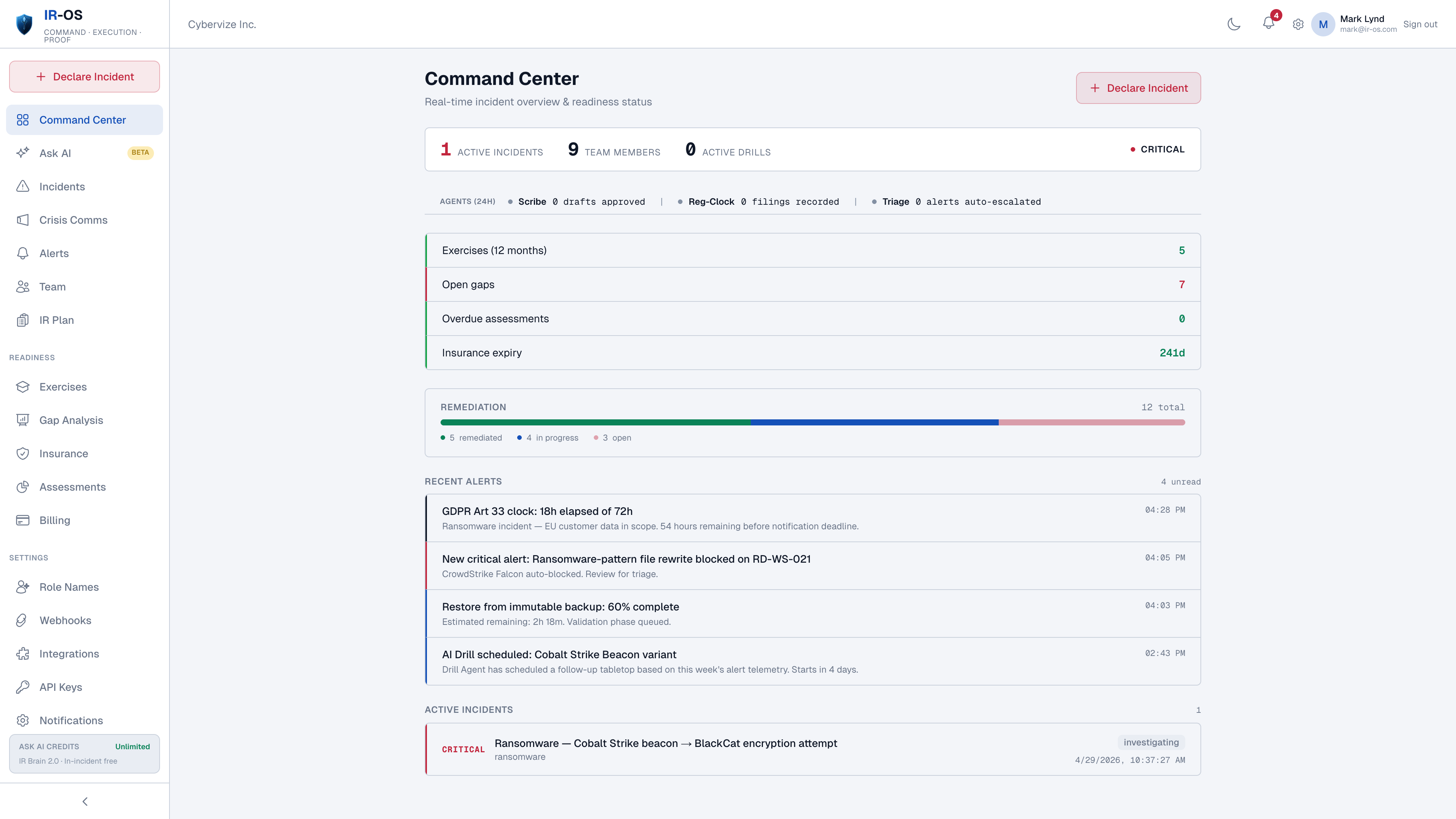
The CISO knows the technical scope. The General Counsel owns disclosure judgment. The CFO owns financial impact. The board needs a defensible record. None of those four views live in the same tool today, and the four-business-day clock does not pause while the team rebuilds a shared picture from screenshots and forwarded emails.
How IR-OS handles SEC cyber incident reporting
Materiality determination capture
Structured inputs (quantitative impact, qualitative factors, investigation status) plus the determination event itself - who, when, rationale - written into the hash-chained ledger.
Four-business-day clock
Clock starts at the determination event, not at detection. Visible to CISO, GC, CFO, and board observer in real time. Counts business days, not calendar days.
8-K disclosure draft
Item 1.05 draft pre-populated from the incident record. Nature, scope, timing language. Counsel of record reviews and signs. IR-OS does not file with the SEC.
Privilege chain
Channel-scoped attorney-client privilege asserted at the org level by counsel of record. Not per-message stickers. Survives discovery.
Amendment workflow
Item 1.05(c) requires amendment when material new information arrives. IR-OS surfaces open determinations and routes the amendment for counsel review with the original disclosure preserved.
Defensible record
Append-only event ledger, SHA-256 chained, Ed25519-signed at incident closure, third-party verifiable at /verify. The artifact you hand to the SEC, plaintiffs' counsel, or D&O carrier on Day 30.
Built from real tabletops with public-company executives
Every workflow on this page reflects what actually happens during a tabletop with a registrant's CISO, General Counsel, CFO, board chair, and outside counsel in the room. The four hardest moments - making the materiality call, holding privilege under regulator scrutiny, handling the amendment when scope changes on Day 6, and producing the record that proves the process - are encoded as default workflow, not as features the team has to remember to use under pressure.
Common questions
What is SEC Item 1.05 and when does the four-business-day clock start?
SEC Final Rule 33-11216, codified as Item 1.05 of Form 8-K, requires public registrants to disclose a cybersecurity incident within four business days of determining the incident is material. The clock starts at the materiality determination, not at detection. IR-OS captures the determination event, who made it, and the rationale, then runs the four-business-day clock from that timestamp.
Does IR-OS draft the 8-K?
IR-OS produces a SEC Item 1.05 disclosure draft for legal review. The draft includes nature, scope, and timing language drawn from your incident record. Counsel of record approves before submission. IR-OS does not file with the SEC. Filing remains the company's responsibility.
How does IR-OS handle the materiality determination?
Materiality is a legal and financial judgment, not an automated decision. IR-OS surfaces the structured inputs the determination requires - quantitative impact, qualitative factors, ongoing investigation status - and captures the determination event itself with attribution, rationale, and timestamp. The hash-chained record makes the determination defensible.
What if a determination later changes?
Item 1.05(c) requires an amendment when previously undetermined or unavailable information later becomes available. IR-OS tracks the open determination and surfaces the amendment workflow when material new information arrives. Both the original and amended disclosures are preserved in the record.
Do CISO, GC, and CFO see the same view?
Each role sees the same source-of-truth incident record with role-scoped lenses. The CISO sees technical scope. The GC sees the privilege chain and disclosure draft. The CFO sees materiality inputs and insurance first-notice status. Sign-offs are hash-chained and visible to all three.