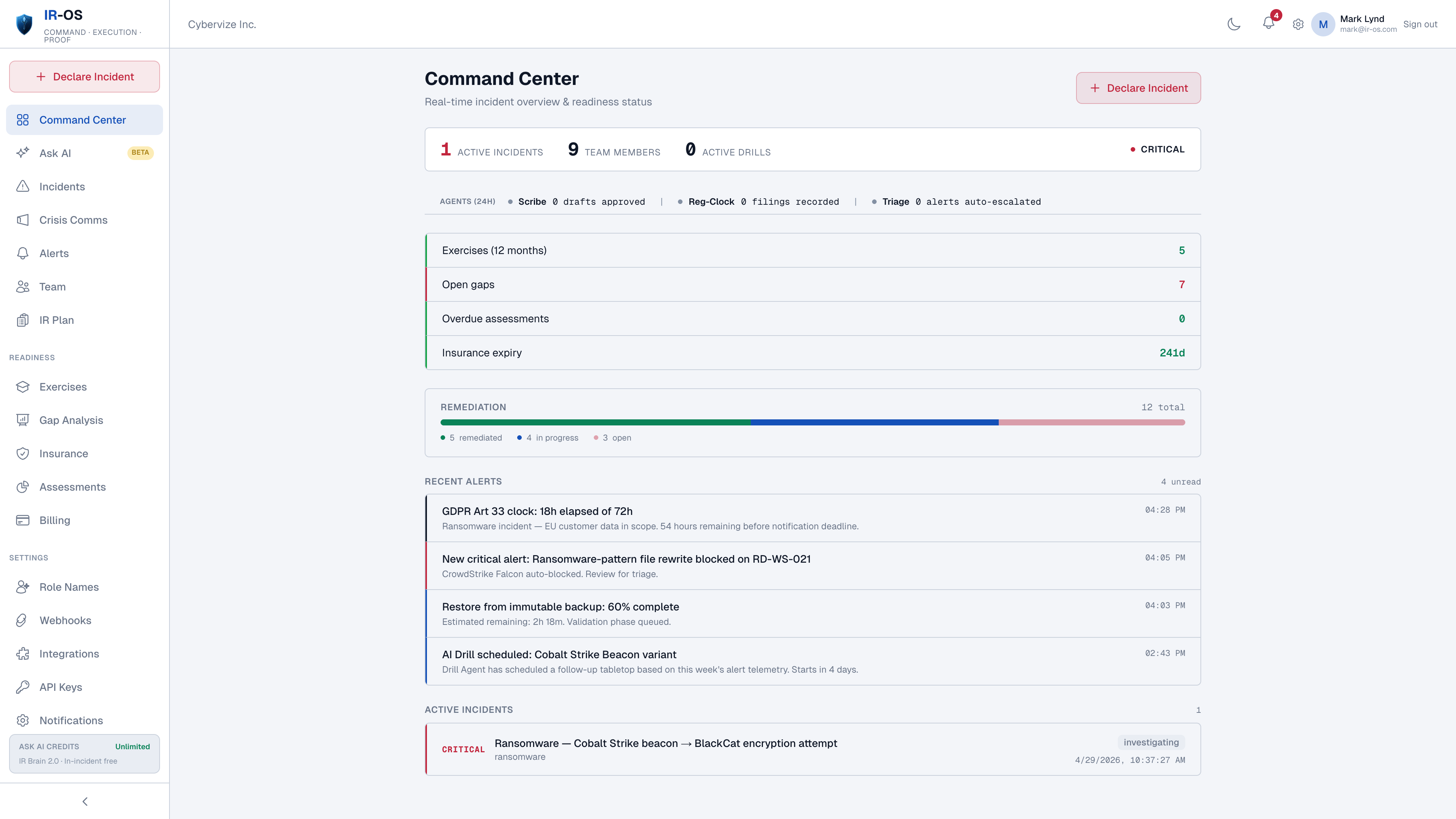
The breach-reporting problem on Day 1
A typical mid-sized breach involves four to seven separate notification obligations running on different clocks with different triggers, different recipients, different content requirements, and different penalties for missing them. The CISO is investigating. The GC is making determinations. The DPO is drafting for the supervisory authority. The CFO is filing carrier first notice. The CCO is preparing state attorneys general. None of those workstreams can wait on the others, and a missed clock is rarely caught in time to remediate.
Every clock IR-OS tracks today
| Regulation / clock | Trigger event | Window |
|---|---|---|
| GDPR Article 33 | Becoming aware of a personal-data breach | 72 hours |
| HIPAA Breach Notification Rule | Discovery of breach (HHS OCR) | 60 days + 60-day individual notice |
| SEC Item 1.05 (8-K) | Materiality determination (registrants) | 4 business days |
| NY DFS Part 500.17 | Determination that an event has occurred | 72 hours |
| NIS2 Directive | Significant incident awareness | 24 / 72 hours / 30 days |
| DORA major ICT incident | Classification as major ICT incident | 4 / 72 hours / 30 days |
| State breach laws (50 US states) | Discovery (most states); some "without unreasonable delay" | 30 to 90 days typical |
| Cyber insurance carrier | Policy-defined trigger; usually first awareness | 24 to 72 hours typical |
| PCI DSS card brands | Suspected payment-card data compromise | Immediately |
How IR-OS handles cyber breach reporting
Parallel regulatory clocks
Each clock runs from its own start event. Visible to CISO, GC, DPO, CFO, CCO, and counsel of record. No dependency between clocks - missing one does not stop the others.
Notification drafts per regulator
Pre-populated drafts per recipient: DPA, HHS OCR, SEC, state AG, NIS2 single point of contact, DORA competent authority. Counsel reviews and signs.
Affected-population tracking
One affected population, fanned out across the jurisdictions it spans. Individual-notification artifacts handed to the breach-notification vendor on the panel firm directory.
Privilege chain
Channel-scoped attorney-client privilege at the org level. Drafts under privilege until counsel of record approves release.
Submission and confirmation capture
Submission events and regulator confirmations recorded back in the incident record. Closes the chain of custody on every notification obligation.
Defensible record
Append-only event ledger, SHA-256 chained, Ed25519-signed at closure, third-party verifiable at /verify. The artifact regulators ask for at the end of an inquiry.
Common questions
Which breach-notification regulations does IR-OS track?
GDPR Article 33 (72 hours), HIPAA Breach Notification Rule (60 days, plus 60-day individual notice), state breach laws across all 50 US states, NY DFS Part 500.17 (72 hours), NIS2 (24-hour early warning, 72-hour notification, 30-day final report), DORA major ICT incident (4-hour initial, 72-hour intermediate, 30-day final), PCI DSS, SEC Item 1.05 (4 business days for public registrants), and cyber insurance carrier first-notice clocks. Other regulations are supported via configurable clock templates on Theater tier.
Each clock has a different trigger - how does IR-OS handle that?
Each regulation has its own start event. GDPR starts on becoming aware. SEC Item 1.05 starts on materiality determination. HIPAA starts on discovery. NIS2 starts on a significant impact. IR-OS captures each start event separately and runs the clocks in parallel. The clocks are not derived from one another - that is the most common cause of missed obligations in breach response.
Does IR-OS submit the notifications for us?
IR-OS produces drafts that counsel reviews and signs off on. IR-OS does not submit to regulators. Submission remains the organization's responsibility, performed through the regulator's prescribed channel (DPA portal, OCR portal, state AG portals, NIS2 single point of contact, etc.). The submission event and confirmation are captured back in the IR-OS record.
What about jurisdictions where individual notification is required?
State breach laws and HIPAA require notification to affected individuals on top of regulator notification. IR-OS tracks the affected-population count, the notification clock for each jurisdiction the population spans, and the notification artifacts (templates approved by counsel, mail merge file, vendor handoff). The actual delivery is performed by the breach-notification vendor on the panel firm directory.
How does the defensible record help during a regulator inquiry?
On Day 90 the regulator wants to see the timeline, the determination, the people in the room, and the chain of custody. The IR-OS record is append-only, SHA-256 hash-chained, Ed25519-signed at incident closure, and verifiable at /verify. The artifact answers the timeline questions before the regulator has to ask them, which compresses inquiry duration significantly.