The decisions the playbook gates
OFAC screening gate
Before any payment discussion, the threat actor is screened against OFAC. Result and analyst captured. Counsel of record routes the decision.
Encryption vs exfiltration
Encryption-only triggers operational recovery. Encryption-plus-exfiltration triggers parallel breach notification (GDPR, HIPAA, state laws, SEC 1.05) and affected-population workflow.
Carrier first-notice and pre-payment
First-notice fires on the policy-defined trigger. Pre-payment authorization gate is wired in before any threat-actor communication.
Evidence preservation
Forensic image capture before remediation. Chain of custody captured. Preserves litigation and regulator-inquiry options.
Communication restraint
External statements held until counsel of record approves. Holding-statement library available for early stakeholder messaging without committing to scope.
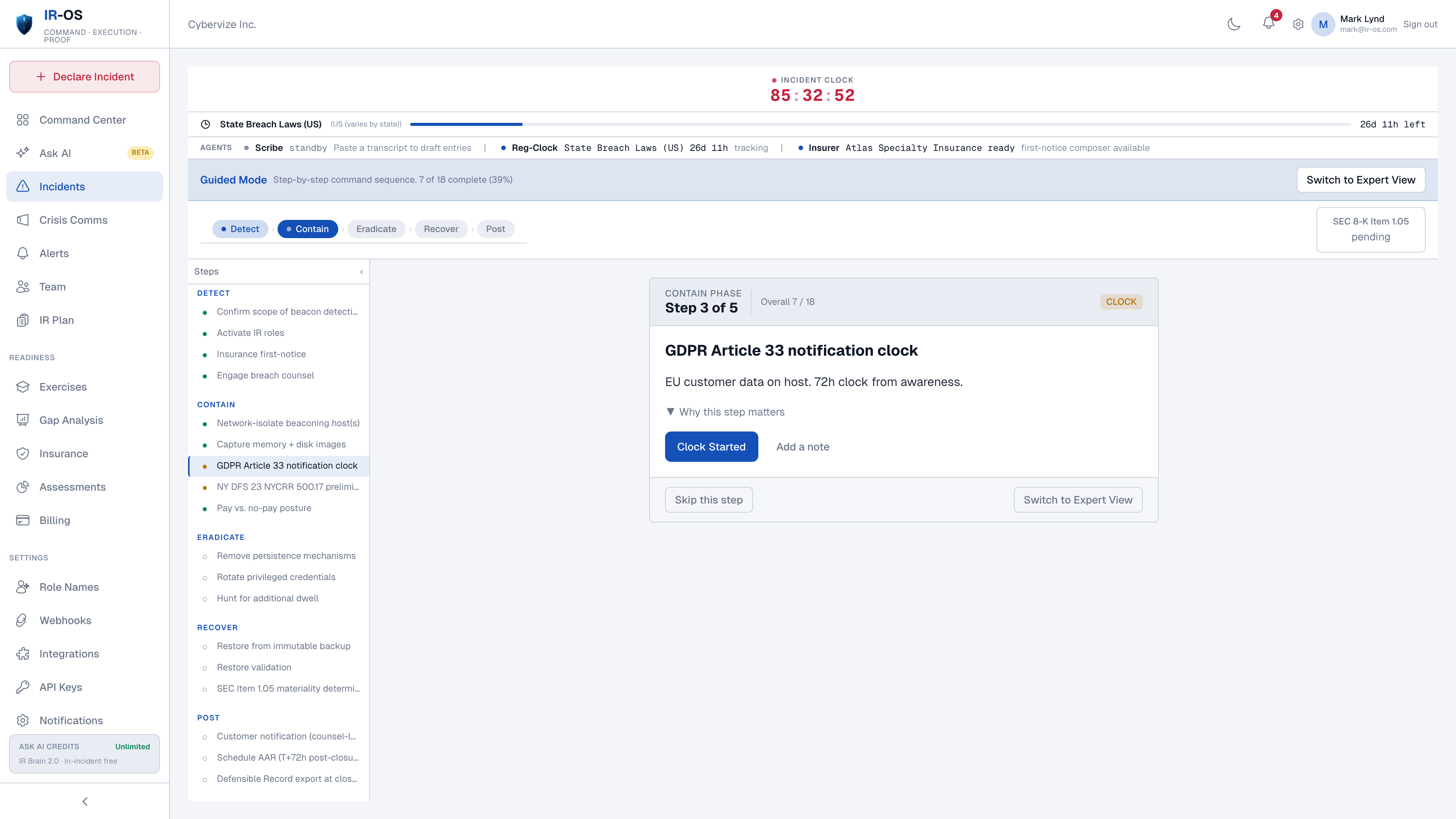
Parallel regulatory clocks
GDPR Article 33 (72 hours), HIPAA (60 days), SEC Item 1.05 (4 business days), state breach laws, NY DFS, NIS2, DORA. Each from its own start event.
Why conditional playbooks matter
The hardest moments in a ransomware incident are not technical. They are the gates. Did anyone screen for OFAC before the negotiator opened a channel. Did the carrier authorize the payment in advance. Was the forensic image captured before remediation overwrote evidence. Did the GC approve the holding statement before the comms lead sent it. A linear playbook treats those as line items the team checks off; a conditional playbook treats them as gates the team cannot pass through without resolving. The hash-chained record makes the resolution defensible on Day 90 when the regulator, the carrier, or plaintiffs' counsel asks.
Common questions
What does the IR-OS ransomware playbook cover?
Conditional branches for the decisions ransomware response actually requires: encryption-only vs encryption-plus-exfiltration, OFAC screening of the threat actor, carrier pre-payment authorization, communication restraint while attribution is uncertain, evidence preservation before remediation, and parallel notification clocks. Each branch is captured in the incident record so the AAR shows which path was taken and why.
Does IR-OS handle OFAC screening?
IR-OS surfaces OFAC screening as a workflow step before any payment discussion, captures the screening result and the analyst who performed it, and routes the decision through counsel of record. IR-OS does not perform sanctions clearance itself - that is the work of counsel and the carrier's panel firm. The platform makes the step impossible to skip and produces the audit trail.
How is the cyber insurance carrier looped in?
Carrier first-notice fires automatically on the policy-defined trigger. Most cyber policies require pre-payment authorization for any ransom payment; that authorization gate is wired into the playbook before any communication with the threat actor. Carrier panel-firm assignments (counsel, forensics, negotiator) are surfaced at the moment they are needed.
What about exfiltration vs encryption-only?
The playbook branches early on the exfiltration determination. Encryption-only ransomware triggers operational recovery. Encryption-plus-exfiltration triggers parallel breach notification (GDPR Article 33, HIPAA, state laws, SEC Item 1.05 if material) and the affected-population workflow. Determinations are captured with rationale and timestamp; amendments are surfaced as new evidence arrives.
Is paying the ransom recommended?
IR-OS does not advise paying or not paying. Payment is a legal, financial, and reputational decision owned by counsel, the carrier, the CFO, and the executive sponsor. The platform surfaces the OFAC screening, carrier authorization, and counsel sign-off gates that any payment decision requires, and captures the decision and rationale in the hash-chained record. CISA and the FBI generally recommend against payment; the platform reflects current guidance from those sources via the IR Brain corpus.