What is IR-OS?
IR-OS is a cyber incident command platform purpose-built for coordinating
the human side of cyber incident response. It handles task assignment,
role-based views, AI-assisted decision support, defensible
timelines, readiness tracking, and after-action reviews, everything
that happens between your SIEM firing an alert and the incident
being closed. It was built from 150+ real C-Suite tabletop
exercises, so every workflow reflects what actually happens under
pressure.
How is IR-OS different from PagerDuty, Jira, or ServiceNow?
PagerDuty routes alerts. Jira tracks tickets. ServiceNow manages
workflows. None of them were built for incident coordination, the
part where executives need status updates, legal needs notification
timelines, comms needs hold/release decisions, and someone has to
prove to regulators what happened and when. IR-OS was built
specifically for that room, by people who have run it 150+ times.
It is not a retrofit, it is purpose-built. See the full
comparison hub for side-by-side breakdowns.
How is IR-OS different from FireHydrant (now part of Freshservice)?
FireHydrant is a strong SRE incident-management platform now
becoming part of Freshservice ITSM via the December 2025 Freshworks
acquisition. For deploys, outages, and infrastructure failures,
that fit makes sense. For cyber incidents with regulators,
insurers, and counsel waiting at the end, it is a structural
mismatch: cyber-IR is a different category than ITSM. Most teams
keep FireHydrant for SRE and run cyber-IR in IR-OS, with a webhook
between them at the classification edge. See the
full comparison or the
migration path.
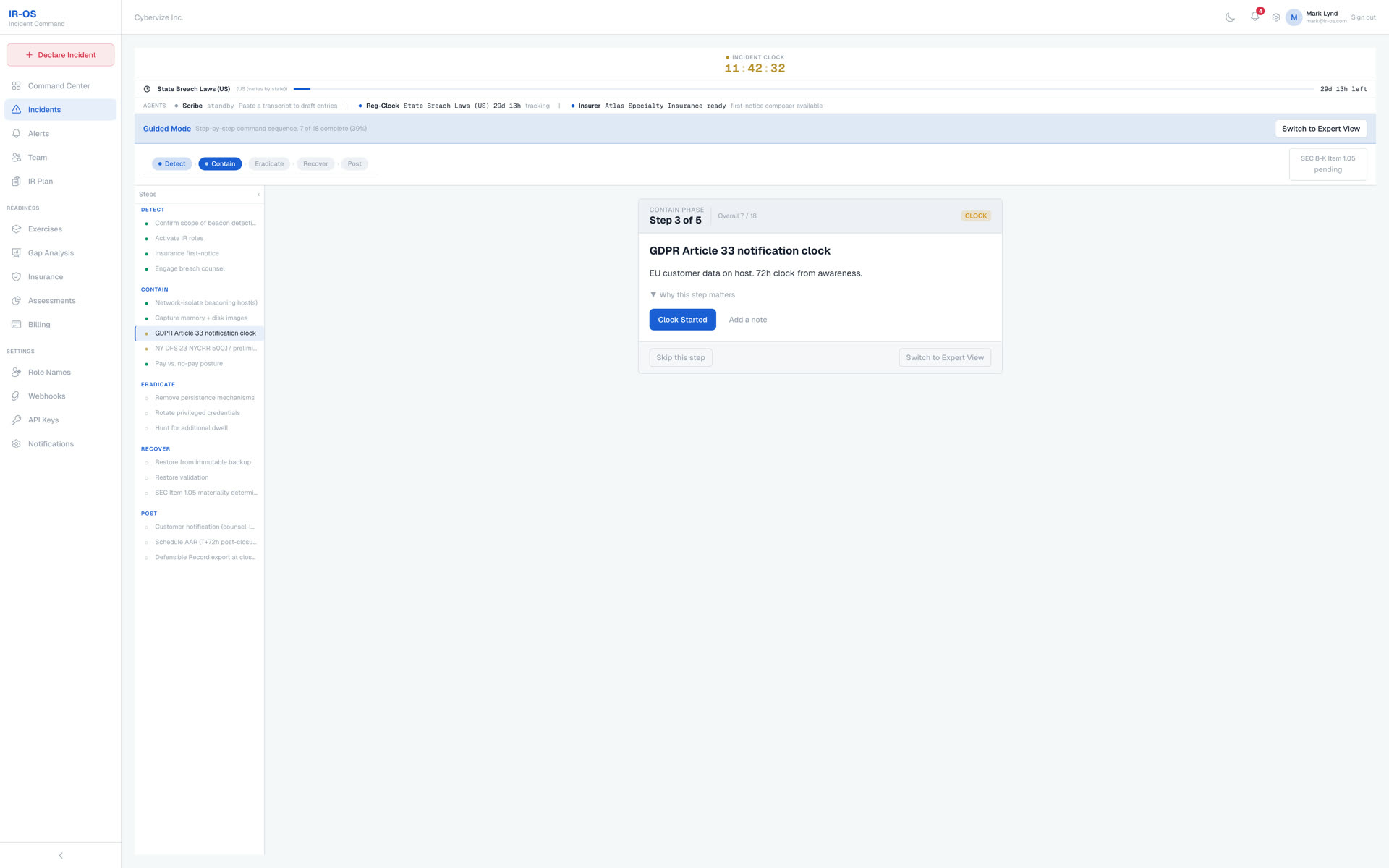
What standards does IR-OS align with?
IR-OS is standards-anchored, not invented. IR plan frameworks
(pick one): NIST SP 800-61 Rev. 2, ISO/IEC 27035-1:2023, CISA
Federal Government IR Playbook, SANS PICERL (SEC504), and IR-OS
Expert (150+ tabletops). Runbook serialization: OASIS CACAO 2.0
with signed export. Threat taxonomy: MITRE ATT&CK and MITRE
D3FEND tagging. Pre-built runbooks derived from the CISA Federal
IR Playbook. Parallel regulatory clocks: SEC Item 1.05, GDPR
Article 33, NY DFS, HIPAA, NIS2, DORA, CIRCIA, state breach laws.
A Standards Watcher Agent on the roadmap monitors these sources
daily and drafts plan amendments within 48 hours of material
changes. See the full list at
#standards.
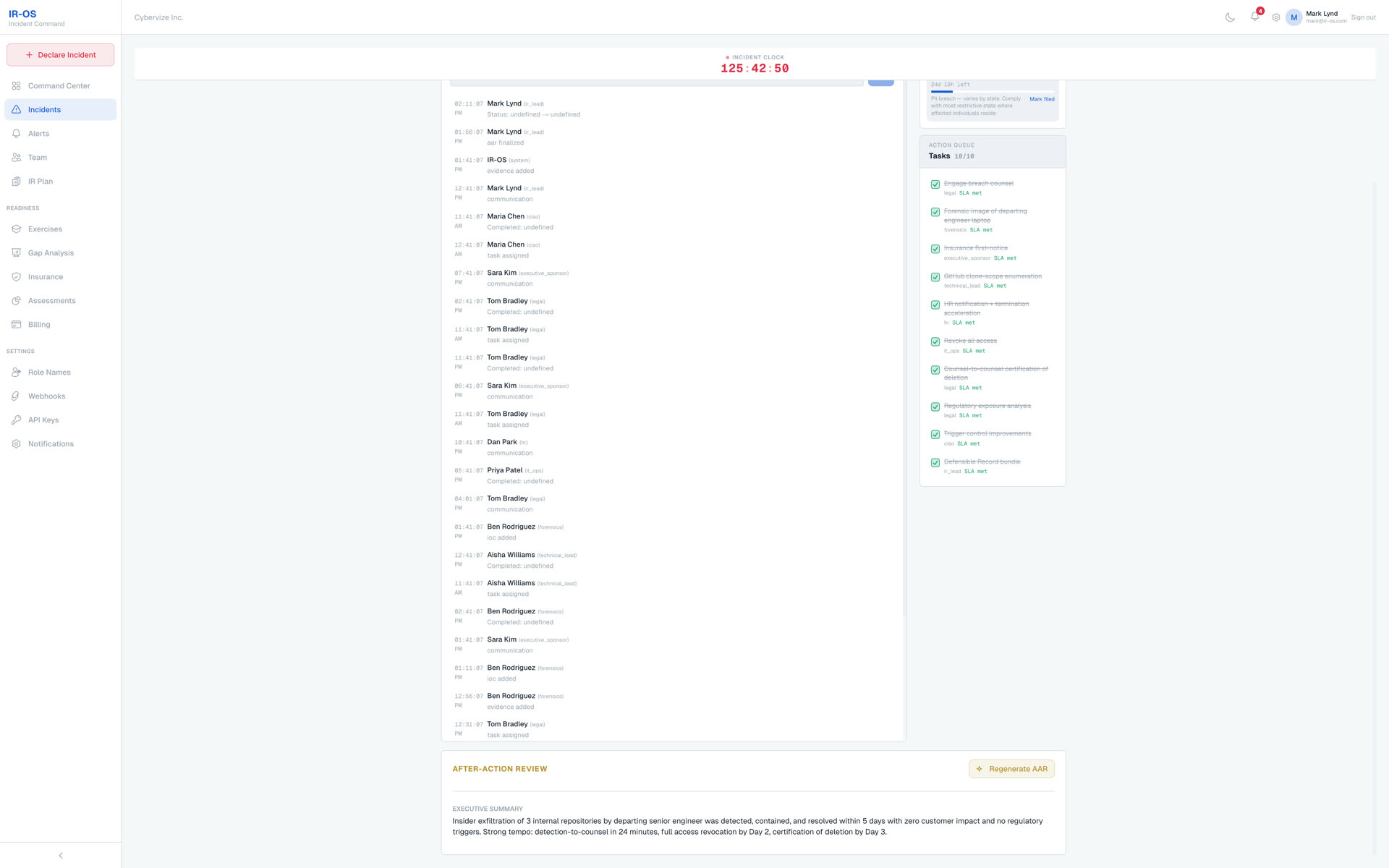
What is a defensible incident record?
Every event in IR-OS is stored in an append-only timeline with
SHA-256 hash chaining. Events cannot be edited or deleted after
creation. Each event is cryptographically linked to the one before
it, creating a tamper-evident chain of custody. This record stands
up to regulatory scrutiny, insurer review, and legal discovery
because it's mathematically provable that no one altered it after
the fact.
How does the AI assistance work?
When you declare an incident, IR-OS reads your IR plan, the incident
type, severity, and regulatory context to generate task suggestions,
notification recommendations, and decision prompts. Every AI
suggestion cites the section of your plan or regulation it's based
on. AI suggestions are advisory, a human approves or dismisses
every one. The system learns from your exercises and incident
patterns to improve over time.
What does "AI-native" mean for IR-OS | isn't every platform
bolting on an AI chat bubble now?
Most platforms add a chat bubble that wraps a generic LLM. IR-OS
is AI-native in a specific sense: (1) every AI surface is
grounded in the IR Brain RAG. NIST 800-61, ISO
27035, SEC Item 1.05, GDPR, CISA, OFAC, MITRE ATT&CK, and 150+
tabletop operational patterns, with inline citations, never
fabrications; (2) the AI surfaces are specialized
, a CISO Copilot, a Comms Copilot, a Compliance Monitor, an
Ask-AI assistant, an AI IRC Recommender, each with its own
guardrailed prompt; (3) IR-OS ships an
MCP (Model Context Protocol) server so Claude
Desktop, Claude Code, Cursor, and any MCP-compatible agent can
query incidents, regulatory clocks, panel vendors, and the IR
Brain natively, no screen-scraping, no CSV exports. The AI isn't
a feature on the side; it's part of the architecture.
Can I connect IR-OS to Claude Desktop or Cursor directly?
Yes. The ir-os-mcp package is a standalone MCP server
that runs locally (via npx) and talks to IR-OS over
HTTPS with a scoped, revocable mcp:read API key you
mint from Settings → API Keys. Six read-only
tools are exposed in v0.1: list incidents, get timeline, compute
regulatory clocks, list panel vendors, read plan phase, and
search the IR Brain RAG. Write tools (declare incident, append
timeline entry) require a separate mcp:write scope
that's on the Phase 2 roadmap with explicit audit-log integration.
What's your security and compliance posture?
IR-OS runs on SOC 2 Type II infrastructure across our edge,
database, LLM, and payment providers, see the Security section
above for the inherited-certifications summary. At the
application layer we enforce strict tenant isolation, a
tamper-evident cryptographic audit trail over governance events,
least-privilege scoped integration keys, hardened identity and
session controls, defense-in-depth across independent layers, and
advisory-only AI surfaces that cannot modify platform state.
Detailed security posture documentation is available to
prospects under NDA at
[email protected].
Can I use IR-OS in a HIPAA or regulated environment?
The underlying infrastructure we run on is HIPAA-eligible when
the relevant BAAs are executed. IR-OS BAAs are available to
enterprise customers as part of the Theater tier or a custom
contract, email
[email protected] to
start that conversation. For regulated customers who need private
IR Brain content (org-specific playbooks, runbooks, regulator
correspondence), the Theater tier supports a private brain
partition distinct from the shared public corpus.
Do I need an existing IR plan to use IR-OS?
No. IR-OS ships with a battle-tested IR plan template built from
150+ real tabletop exercises. You can use it as-is, customize it to
your organization, or upload your own plan. The platform adapts its
AI suggestions and task generation to whatever plan you have in
place.
How long does setup take?
Most teams are operational in 15 minutes. Import your team roster,
choose or upload your IR plan, set notification preferences, and
you're ready to declare your first incident or run your first
tabletop exercise. There's no weeks-long implementation or
professional services engagement required.
What types of incidents does IR-OS handle?
Data breaches, ransomware, insider threats, system outages,
third-party compromises, physical security events, and regulatory
incidents. Each incident type has tailored workflows, task
templates, notification sequences, and regulatory mappings. You can
also create custom incident types with your own workflows.
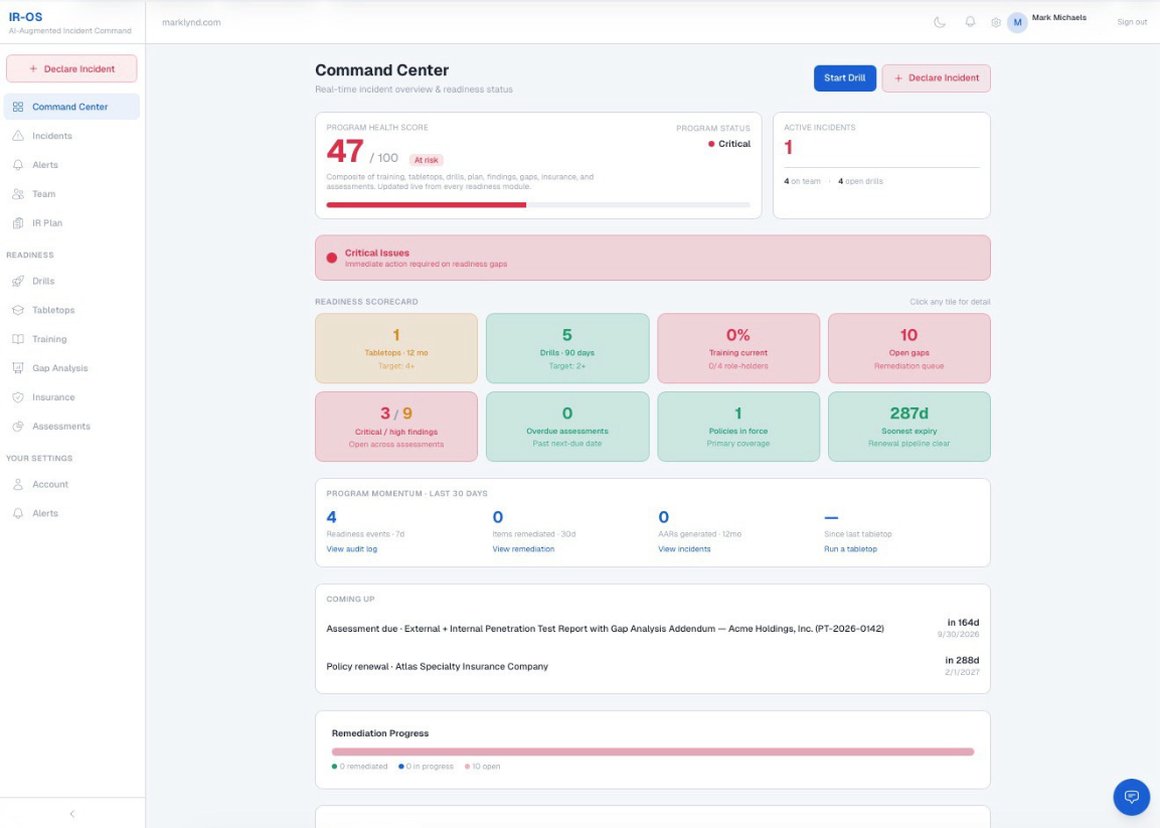
How does the readiness dashboard work?
Four traffic-light indicators track your organizational readiness:
exercise compliance (have you tested recently?), open remediation
gaps (from exercises, assessments, and AARs), overdue assessments,
and insurance expiry. Green means ready. Amber means attention
needed. Red means act now. It gives leadership a single-glance view
without digging through multiple reports.
Can I run tabletop exercises in IR-OS?
Yes. Log exercises with attendees, scenarios, findings, and action
items. Every finding automatically creates a remediation item in the
gap tracker. Over time, IR-OS builds a complete picture of your
readiness posture by connecting exercises, assessments, real
incidents, and after-action reviews into one continuous improvement
loop.
What happens after an incident closes?
IR-OS auto-generates a structured after-action review (AAR):
executive summary, timeline summary, what worked well, gaps
identified with severity ratings, SLA compliance analysis,
regulatory compliance status, and prioritized recommendations. Each
identified gap can be pushed to the remediation tracker with one
click, closing the loop from incident to improvement to
verification.
Is my data secure?
IR-OS enforces strict tenant isolation at the database layer
every query is bound to the caller's organization before any row
returns. Data is encrypted at rest and in transit. The
append-only event store ensures no one, including administrators
, can alter the incident record after creation. Your incident
data never leaves your isolated tenant. Full security posture
documentation available under NDA at
[email protected].
What's the trial and guarantee?
Every plan. Squad, Command, and Theater, includes a
7-day free trial and a
30-day money-back guarantee. If IR-OS doesn't
measurably improve your incident coordination and readiness workflow
within 30 days, we'll refund your payment in full. No questions, no
frictionrequired for the trial.
Do you offer discounted pricing for first responders or SLED?
Are you a first responder, fire, EMS, or law enforcement agency? You
may qualify for discounted pricing, contact us and we'll take care
of you. Also, state/local government, K-12, and higher ed is
available upon request, you must
reach out to us.