The DORA three-stage clock
4-hour initial notification
Initial classification, severity assessment, services and clients affected, ongoing investigation indication. Pre-staged template per entity type.
72-hour intermediate report
Updated impact, root-cause hypothesis, mitigation actions in flight, cross-border or supply-chain dependency surfacing.
One-month final report
Confirmed root cause, full impact (financial, operational, client, reputational), remediation status, lessons-learned summary.
Article 18 classification
Seven-dimension classification inputs surfaced for legal and risk: clients affected, reputational impact, duration, geographical spread, data losses, criticality, economic impact.
Competent authority submission
Submission event captured per authority. Cross-jurisdiction fan-out for entities with passported activities. Confirmation events captured back.
Parallel regulatory clocks
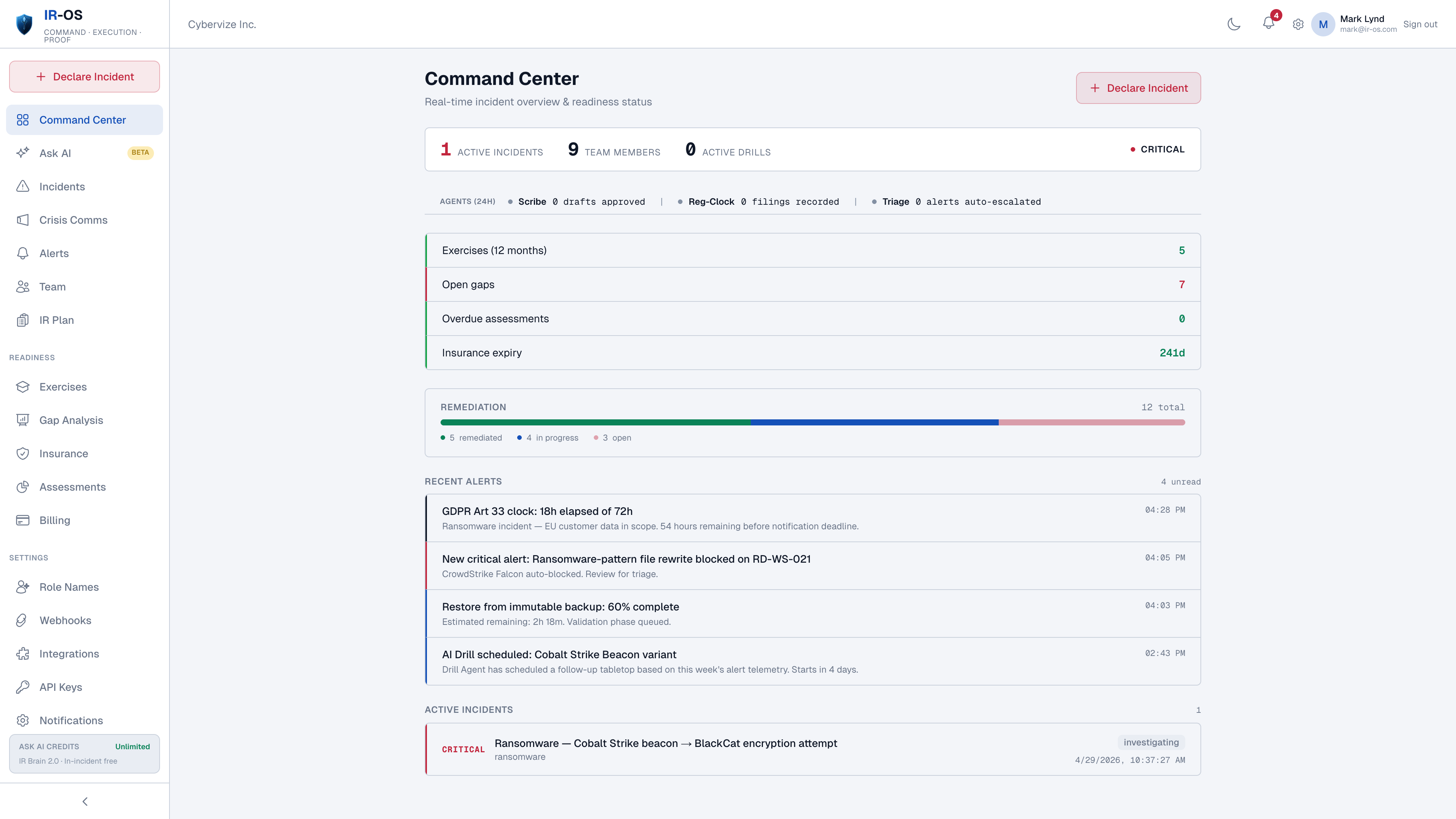
DORA alongside NIS2 (where in scope), GDPR Article 33, sector regulators, and cyber insurance first-notice. Each from its own trigger event.
The financial-entity reporting workflow
The hard part of DORA is not the four-hour stage in isolation. The hard part is producing a counsel-reviewed initial notification within four hours of classification, while the technical investigation is still in motion, while NIS2 may also be in scope, while GDPR Article 33 may also be running for personal-data aspects, and while the carrier first-notice clock is firing. IR-OS pre-stages the templates, runs the clocks in parallel without dependency, and captures every submission and confirmation in the hash-chained record. Day-30 audit trail is exportable for the competent authority, the management body, or the supervisory examination team.
Common questions
What does DORA require for major ICT incident reporting?
DORA (Regulation (EU) 2022/2554), Article 19, requires financial entities to report major ICT-related incidents to their competent authority on a three-stage clock: an initial notification within four hours of classification (or by end of business day, whichever is sooner), an intermediate report within 72 hours, and a final report within one month. The reporting templates and content requirements are specified in the Commission Delegated Regulations and the supervisory technical standards.
Who is in scope for DORA?
DORA applies to a broad set of EU financial entities: credit institutions, payment institutions, electronic money institutions, investment firms, crypto-asset service providers, central securities depositories, central counterparties, trading venues, trade repositories, AIFMs, UCITS management companies, insurance and reinsurance undertakings, and ICT third-party service providers serving these entities. The scope and applicable thresholds vary by entity type.
How is a major ICT incident classified under DORA?
Article 18 of DORA, expanded by the Joint Committee guidelines and Commission Delegated Regulation, defines major ICT-related incident classification criteria across seven dimensions: clients and counterparties affected, reputational impact, duration, geographical spread, data losses, criticality of services, and economic impact. A combination of severity and impact thresholds determines the major-incident classification. IR-OS surfaces the classification inputs for the legal and risk teams to assess and captures the determination event.
Can DORA reporting and NIS2 reporting share an incident record?
Yes. The same incident record runs the DORA three-stage clock alongside the NIS2 three-stage clock, GDPR Article 33, sector-specific regulators, and cyber insurance first-notice. Many financial entities are subject to both DORA and NIS2; the platform runs the clocks in parallel without dependency between them. Submissions to each authority are captured separately.
Does the platform support reporting to ESAs and the Oversight Forum?
DORA reporting goes to the financial entity's competent authority, which then transmits the relevant information to the ESAs (EBA, EIOPA, ESMA), the ECB where applicable, and the Single Resolution Board. IR-OS produces the counsel-approved draft for the competent authority. Onward transmission within the supervisory ecosystem is the competent authority's responsibility. The platform captures submission and confirmation events back in the incident record.