What the executive war room needs
Stakeholder map
Internal (employees, board), external (regulators, customers, partners, media, carriers), with messaging templates and approval routing per audience.
Holding-statement library
23 attorney-shape templates for the most common cyber-crisis moments. Watermarked SAMPLE exports for tabletops. Privileged drafts under counsel review.
Parallel regulatory clocks
GDPR, HIPAA, SEC Item 1.05, NY DFS, NIS2, DORA, state breach laws, carrier first-notice. Each from its own start event. Visible to the war room in real time.
Privilege chain
Channel-scoped attorney-client privilege at the org level by counsel of record. Drafts under privilege until counsel approves release. Survives discovery.
Hash-chained sign-off trail
Every external statement, regulator submission, and material decision signed off by counsel and captured in the append-only ledger. SHA-256 chained.
Board-observer access
Read-only briefing for board chair and audit committee. Plain-language summary. Materiality inputs visible. Privileged drafts hidden.
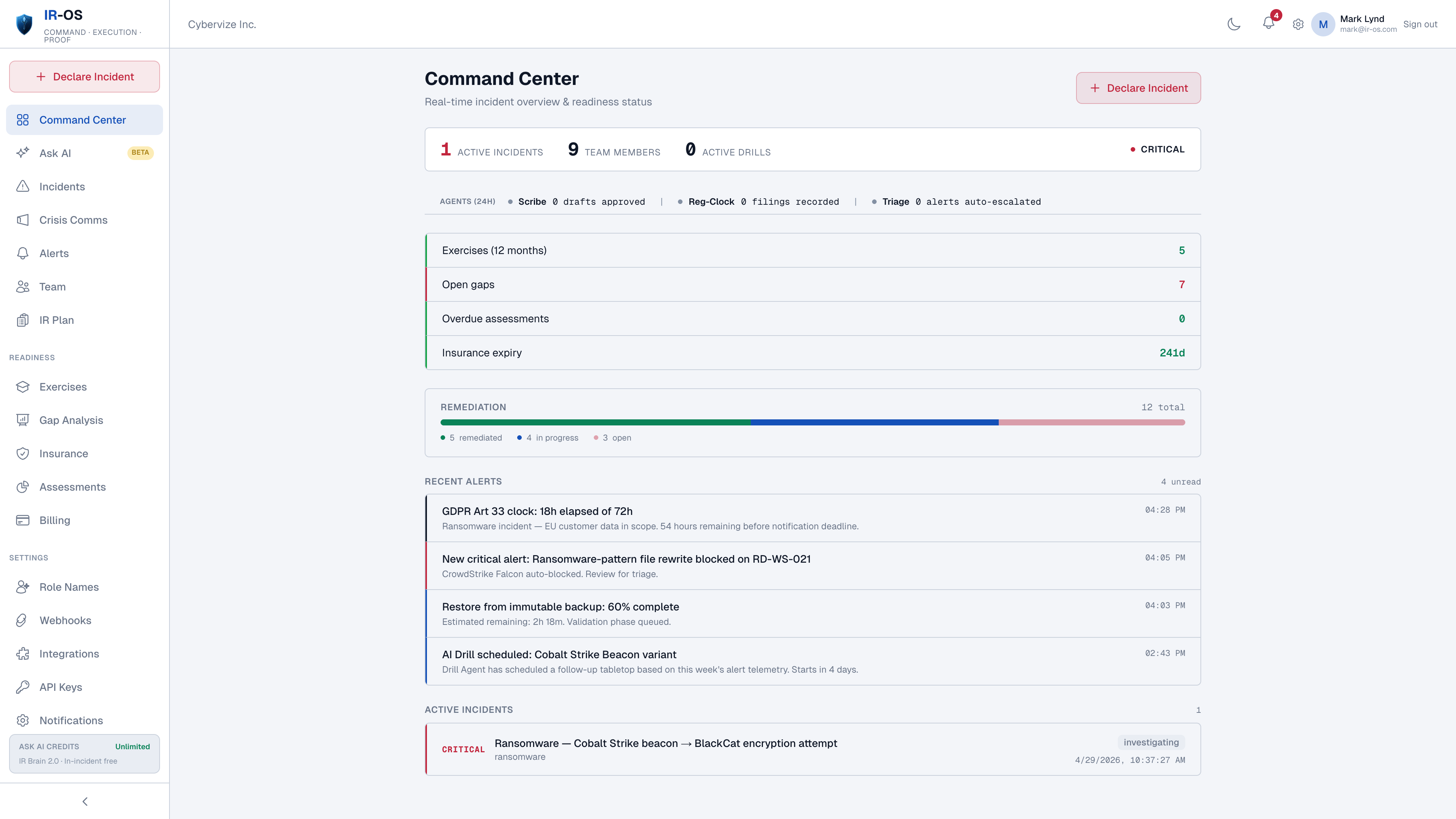
The war-room model in practice
A major cyber crisis runs in parallel through six workstreams: technical investigation, legal determination and disclosure, executive communications, financial impact and insurance, customer and partner notification, and board reporting. None of those workstreams can wait on the others, and a missed handoff between them is the most common cause of a crisis turning existential. The platform model is to make each workstream visible to the others in real time, encode the handoffs as ledger events, and capture every sign-off in a chain that the audit committee, the regulator, and the D&O carrier can verify after the fact. That is the difference between a war room that produces a defensible record and a war room that produces a chaos of forwarded emails.
Common questions
What is a cyber crisis management platform?
A cyber crisis management platform is the executive war-room software for a major cyber incident. It is the command surface CISOs, General Counsel, CFOs, board observers, and outside counsel use during a crisis: stakeholder map, holding-statement library, parallel regulatory clocks, hash-chained sign-off trail, panel-firm directory, and a defensible record. The platform owns the executive coordination layer that ticketing tools and SRE-IR tools cannot.
How does this differ from a generic crisis management tool?
Generic crisis management tools cover natural disasters, product recalls, and PR events. Cyber crisis is different: parallel regulatory notification clocks (GDPR, HIPAA, SEC Item 1.05, NY DFS, NIS2, DORA), structural attorney-client privilege, cyber insurance carrier first-notice, OFAC screening, evidence preservation, and a hash-chained record that survives regulator inquiry. None of those are generic-crisis features. IR-OS is built specifically for cyber-shaped crises.
Who logs in during a cyber crisis?
Six pre-defined IRC roles plus a board-observer role. Incident Commander (often the CISO or IR Lead). Scribe (captures the timeline). Communications Lead (VP Comms or PR). Legal Liaison (General Counsel or DPO). Technical Lead (security engineering). Executive Sponsor (CEO or COO). Board observer is read-only with privileged drafts hidden. Outside counsel of record can be added with assertion-level privilege scope.
How does the platform handle attorney-client privilege?
Privilege is asserted at the org level by counsel of record, applied as a channel-scoped attribute, and inherited by all communications and drafts within scope. Per-message privilege stickers do not survive discovery; the IR-OS model does. Privileged drafts under counsel review are hidden from board observer and non-privileged staff. Privileged scope is captured in the hash-chained record.
What artifact is produced at the end of a cyber crisis?
A complete, append-only, SHA-256 hash-chained, Ed25519-signed record covering decisions, determinations, regulator submissions, carrier first-notice, panel-firm engagements, signoffs, the AAR, and gap remediation. Verifiable at /verify by any third party with the public key. This is the artifact regulators, plaintiffs counsel, and D&O carriers ask for. The board exports it for the audit committee meeting.